stuxnet
-

Islamic Republic Authorities Claim Blackout Was The Work Of Israeli Sabotage
It certainly looks like Israel just cyber attacked Iran again. Authorities with the Islamic Republic are claiming that a blackout at one of the nation’s top nuclear facilities is the result of Israeli sabotage, and an Israeli media outlet has similarly claimed that the attack may have been the work of the intelligence agency Mossad.
-

The World’s First Firmware Worm For Mac Is Here, And It Sounds Scary
“Oh don’t worry,” your uncle said when you were shopping for a new computer. “Macs are virtually virus-proof.” Your uncle was wrong.
-

A Cyberattack Caused Real-Life Chaos At A German Steel Mill
At this point, it’s obvious that cyberattacks can have devastating, far-reaching consequences. Look at the fallout from the Sony hack. But it’s still very rare for digital aggression campaigns to cause direct physical damage, which is why a recent cyberattack that screwed with a blast furnace at a German steel mill is so disturbing.
-

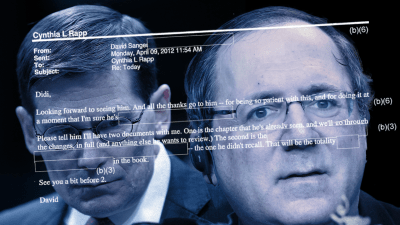
Did A USB Stick Infect A Russian Nuclear Plant With Stuxnet?
There’s a common misconception that you need to be connected to the internet to get infected with malware. Well, that’s not true and, according to renowned cybersecurity expert Eugene Kaspersky, the folks at a nuclear power plant in Russia learned this the hard way.