security centre
btyb
-

Giz Explains: Why You Should Be Using A VPN
For as ubiquitous as connectivity has become and how reliant we’ve grown on it, the internet is still a digital jungle where hackers easily steal sensitive information from the ill-equipped and where the iron-fisted tactics of totalitarian regimes bent on controlling what their subjects can access are common. So instead of mucking around in public…
-

Forbes Reporter Remotely Hacks Smart Homes
The connected house you can control from the internet or your smartphone? They might be called a smart homes, but some of them have some very dumb vulnerabilities. In fact, some of the houses made smart by a company called Insteon were insecure enough that a Forbes reporter could hack them from the comfort of…
-
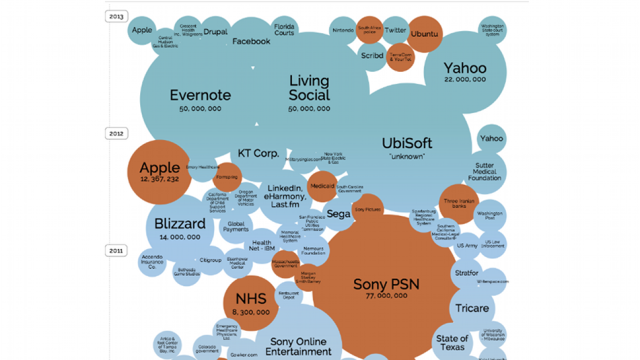
The World’s Biggest Data Breaches, Visualised
It sometimes feels like there’s a big data breach in the news every week — but some are far worse than others. This data visualisation shows the world’s biggest data breaches to date, and how they compare over time.
-
Why Doesn’t Skype Protect You Against Eavesdropping?
Skype has long claimed to be “end-to-end encrypted”, an architectural category that suggests conversations over the service would be difficult or impossible to eavesdrop upon, even given control of users’ internet connections. But Skype’s 2005 independent security review admits a caveat to this protection: “defeat of the security mechanisms at the Skype Central Server” could…