A ransomware gang called “Cuba” claims to be selling off data on the dark web belonging to Automatic Funds Transfer Services (AFTS), a Seattle-based financial services and data management firm that suffered a bad ransomware attack in early February.
This is quite alarming, given that the California Department of Motor Vehicles announced yesterday that it is a longtime client of AFTS and that the February attack may have compromised approximately 20 months of data it had shared with the company, including the “names, addresses, licence plate numbers and vehicle identification numbers (VIN)” of millions of Californians.
[referenced id=”1673500″ url=”https://gizmodo.com.au/2021/02/california-dmv-warns-millions-of-records-may-have-been-exposed-in-worrisome-data-breach/” thumb=”https://gizmodo.com.au/wp-content/uploads/2021/02/19/lrbrcwsyse18mpvhrmkz-300×169.jpg” title=”California DMV Warns Millions of Records May Have Been Exposed in Worrisome Data Breach” excerpt=”The California Department of Motor Vehicles has warned state residents that over a year’s worth of data — including customer addresses and licence plate numbers — may have been compromised in a recent cyberattack on a third-party contractor.”]
As noted in our previous coverage, the California DMV is not the only government agency that uses AFTS. About a dozen public entities in communities across Washington state have already made similar announcements: this includes Seattle, Kirkland, and Redmond, among many others. Many of these agencies used the firm for bill pay services, meaning that, in some cases, there is a possibility financial information may have been stolen.
It is unknown how many clients AFTS actually has, or how many entities are believed to have been affected by the attack. What is known is that the firm handles sensitive financial information for many of its clients, and that “Cuba” now claims to be selling “financial documents, correspondence with bank employees, account movements, balance sheets, and tax documents” that were compromised in the attack.
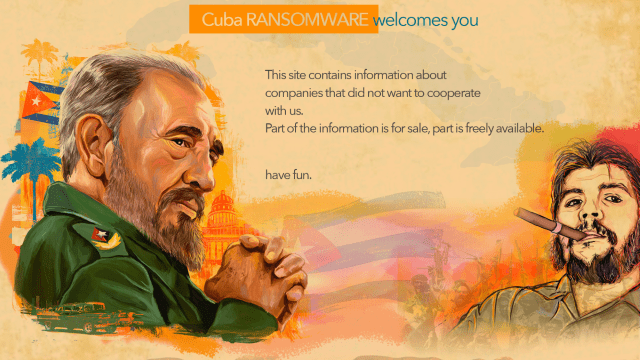
All of this can be viewed on Cuba’s dark web “leak site,” where AFTS data is listed as “paid content”:
“Cuba” has also posted data tranches from a number of other organisations, offering them up for free. This is a common tactic used on ransomware sites. Much like a Patreon page where a gig artist or writer may offer you a few clips for free to encourage you to subscribe, dark web sites offer free content to help legitimate the paid content, proving it’s worth shelling out money for their more exclusive material.
Threat analyst Brett Callow, who works for security firm Emsisoft, said that “Cuba” only recently started publicizing its alleged hacks. The group’s leak site was likely launched “earlier this month or late January,” said Callow, in an email to Gizmodo. “Interestingly, it seems that the group may have started stealing information much sooner, as one of the leaks appears to relate to an attack that was carried out in November 2019,” he said.
When reached by phone Thursday, an AFTS representative said that the company had hired a digital forensics firm to investigate the attack and that state and federal law enforcement were also assisting. The company has no further updates at this time, he said.