Whether we’re talking about the Obama administration or the Trump era, the position of U.S. law enforcement agencies has been that tech companies need to give authorities a backdoor into encryption. The infosec community agrees that this would just make us all less safe. Along the way, we’ve known that cops use expensive devices to break into encrypted phones but have had little visibility into the practice. Now, a new study is giving us some insight into the murky world of mobile device forensic tools (MDFT) and their widespread use in criminal cases.
Upturn, a non-profit focused on the use of technology by police, used over 110 public records filed with law enforcement departments across the country to put together the most in-depth study of MDFTs we’ve seen to date. Among its revelations, the report finds that most, if not all, police departments have access to a phone-hacking tool, and “at least 2,000 agencies have purchased a range of products and services” from a variety of vendors with names like Cellebrite, Grayshift, MSAB, Magnet Forensics, and AccessData.
If you’re only vaguely familiar with MDFTs, you’ve probably seen photos of the GrayKey device going around but we don’t know much about them. The basic concept is that the tools use some combination of exploiting security vulnerabilities and brute force password-guessing to gain access to private material.
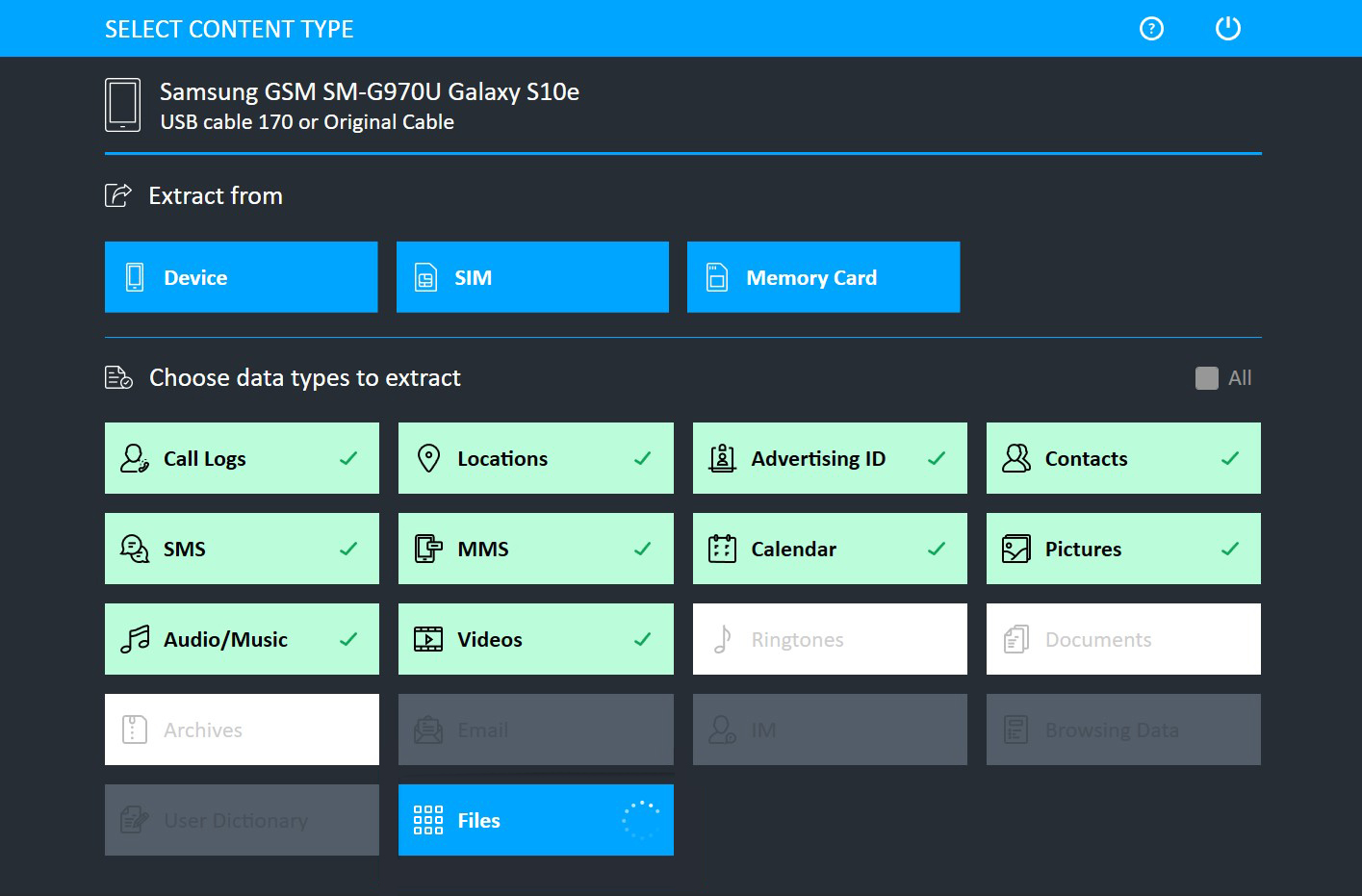
According to Upstart, large vendors include support for thousands of phones in their MDFT systems. In each case, they might take advantage of an unpatched security hole that’s specific to the device being searched or exploit a flaw that exists across a range of products. Accessing phones can be accomplished through four main methods with different benefits. Based on public records, Upstart says Cellebrite offered one form of access, logical extraction, for 8,393 devices back in 2016. Apple products are known for being a tough nut for hackers to crack, but Cellebrite was offering support for iOS 13 three weeks after its release. And the “checkm8″ vulnerability that was announced in 2019 showed that a hardware flaw could be used to break into hundreds of millions of iPhones.
Yes, that’s all disturbing, but it’s really a demonstration of how many “backdoors” already exist in encrypted devices. What we’re talking about is hacking services, plain and simple. Cellebrite isn’t the only one that’s aware of these security flaws, it’s not even the only competitor in the phone-cracking-for cops business. Whenever the House or U.S. Senate or attorney general argue that they need a permanent backdoor into a company’s products, they’re really arguing for the creation of a giant security hole that every bad actor knows about, including the police.
Since 2014, U.S. law enforcement agents have been required to seek a warrant when they want to search a phone in the course of the investigation, but Upturn found that many people just allow searches to happen voluntarily. As MDFTs become more widely available, courts became more accustomed to issuing warrants and investigations increasingly relied on digital forensics, and the number of phone searches has exploded. Upturn was able to determine that at least 50,000 data extractions were conducted by 44 law enforcement agencies between 2015 and 2019. That’s 44 out of the 2,000 agencies that were found to be using the cracking systems. Lack of tracking and a refusal to hand over data was cited as the reason for our inability to get more accurate figures from authorities.
In all, Celebrite told the New York Times that it counts 7,000 customers in 150 countries — and that’s just one vendor. Not everyone is dropping $US150,000 ($210,675) for their own top-of-the-line MDFT, as the Dallas Police department reportedly did. Some departments simply call in a favour from another agency and à la carte services are available to send off a particularly difficult device for cracking. And, at this point, we’re way beyond confining these searches to terror plots and other major crimes. Records showed that data extraction was conducted over crimes that include marijuana possession, graffiti, shoplifting, public intoxication, prostitution, vandalism, car crashes, parole violations, and petty theft. In one warrant obtained by Upturn researchers, a device search was approved in a case involving a fight over $US70 ($98) at a McDonalds.
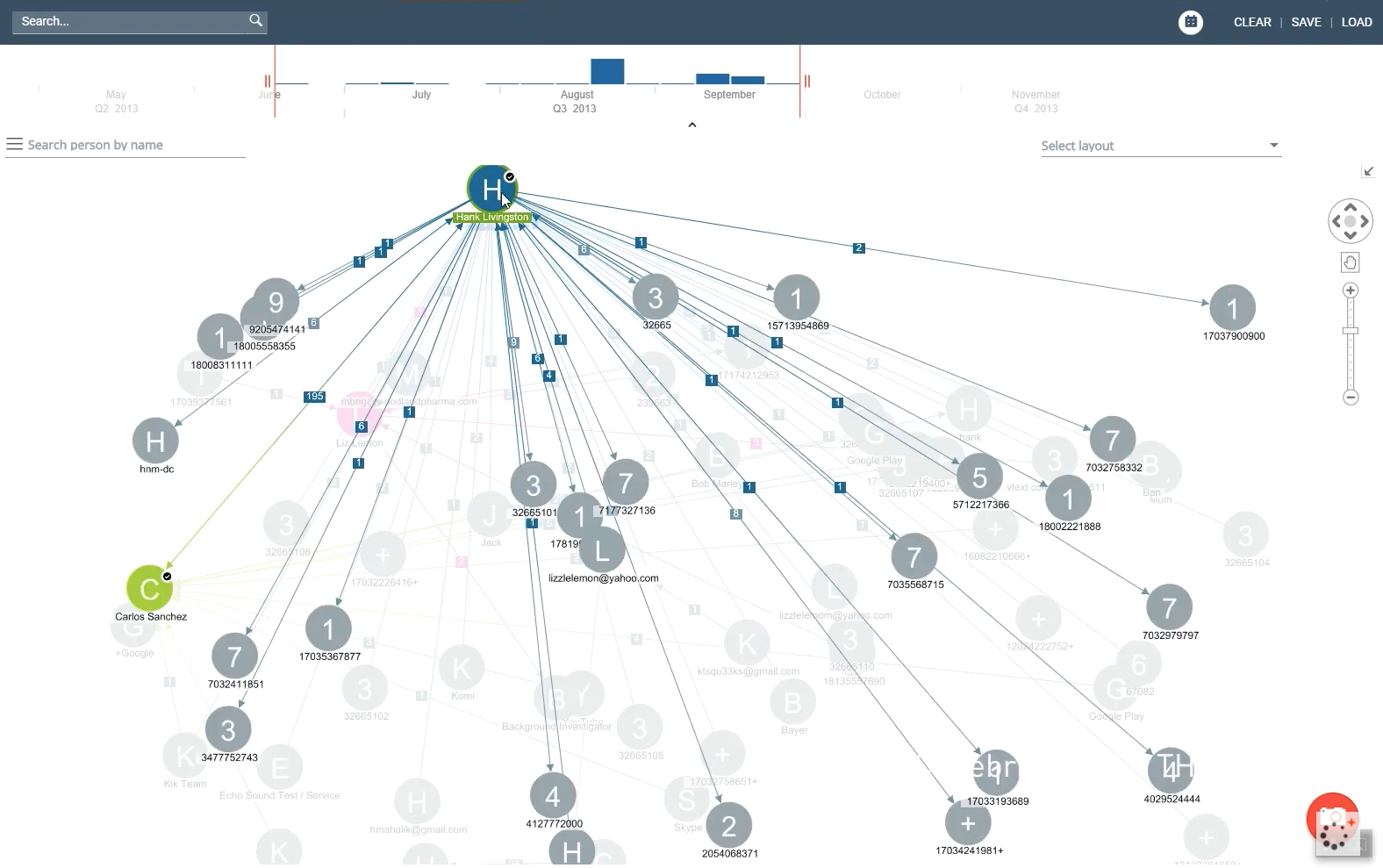
Even when suspects/witnesses/persons of interest do grant permission for a search of their device, they may be unaware of just how much data they could potentially be giving away. Deleted data can still be recovered, location history can be downloaded from Google, and cloud data can be accessed and pulled from servers through the phone. Many MDFT vendors offer surprisingly robust analytics tools to help cops cut through the noise and some even offer data comparisons between multiple devices. An innocent suspect could easily think that there’s nothing incriminating on their personal device, but prosecutors might end up painting an entirely unexpected picture from overlapping forensic evidence.
With off-the-charts cop enthusiasm, devices going for six figures, and a small field of competition, it’s clear that MDFT vendors are an ally in the fight against special encryption backdoors — too many not-so-special backdoors already exist that are wildly profitable.
