The DOJ and FBI have been in a bit of a cold war with Apple and the tech community ever since the controversy in 2015 over unlocking the San Bernardino shooter’s iPhone. This week, the war heated up again with the FBI and Apple exchanging words about encryption, and today, the Deputy Attorney General of the United States stepped into the fray.
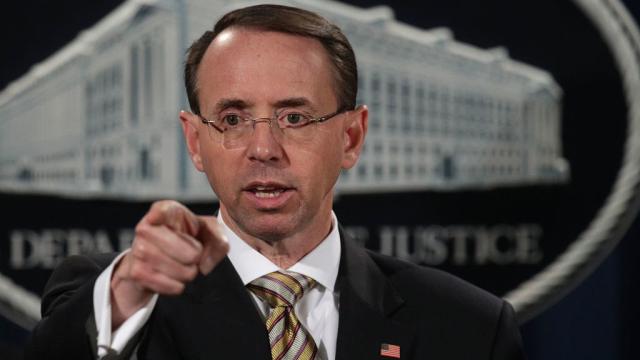
Photo: Getty
[referenced url=”https://gizmodo.com.au/2017/11/the-fbi-is-seeking-access-to-the-sutherland-springs-shooters-iphone/” thumb=”https://i.kinja-img.com/gawker-media/image/upload/t_ku-large/dod3w36ax4ftrk250qfo.jpg” title=”The FBI Is Seeking Access To The Sutherland Springs Shooter’s iPhone” excerpt=”The Federal Bureau of Investigation apparently missed a key window in which they could have sought Apple’s assistance with accessing data on an iPhone used by the Sutherland Springs shooter.”]
The FBI is currently investigating the circumstances surrounding the shooting of 26 people at a church in Sutherland Springs, Texas. The shooter, Devin Kelley, is dead, so law enforcement has had to work with what evidence he’s left behind. On Tuesday local time, FBI special agent Christopher Combs gave a press conference in which he lamented the fact that the FBI has, so far, been unable to unlock Kelley’s phone. The next day, Apple let the world know that it may have been able to help, but the FBI waited more than 48 hours to inform Apple or the public that it was trying to unlock an iPhone. At a minimum, Apple said that it could’ve suggested trying the Touch ID feature in that 48 hours, but it’s too late now.
That could have been the end of the story. Until today, neither the FBI nor Apple has seemed to want to jump back into the heated debate on encryption that occurred in 2015. People from the FBI and DOJ have continued to make comments that they need a backdoor into encryption, but without a major case such as San Bernardino to win over public sentiment, they haven’t made a huge public deal out of it. And Apple has been happy to walk away from that incident without being forced to create future backdoors for the US government. It would appear that Apple’s statement on Wednesday was an effort to nip a new uproar in the bud. But today, Deputy AG Rod Rosenstein brought the subject up once again. Rosenstein (conveniently) did not mention that Apple publicly shamed the FBI for not even attempting to approach the company for help.
At a breakfast for business leaders in Maryland, Rosenstein gave a wide-ranging speech that touched on the importance of law before politics, the increasing problem of cybercrime, and once again, how much he’d love to be able to get into anyone’s phone whenever he has an investigation. Rosenstein is clearly being either wilfully ignorant or he’s gassing the public when he makes statements such as, “nobody has a legitimate expectation of privacy in that phone,” referring to the shooter’s phone. “The suspect is deceased, and even if he were alive, it would be legal for police and prosecutors to find out what is [on] the phone,” he explained.
The FBI, and other government agencies around the world, tend to make their case for a backdoor into encryption based on either the need to protect the public or some sort of fine legal argument about warrants. Rosenstein went with both. “When you shoot dozens of American citizens, we want law enforcement to investigate you,” he told the attendees. “There are things we need to know.”
As always in this argument, the issue is that no one’s talking about the privacy of a dead man, or the constitutionality of a search warrant for the phone, or even anyone’s physical safety. Opponents of governmental backdoors are talking about the privacy and safety of everyone who uses technology and the internet. Good encryption means no one can have a backdoor. If there’s a backdoor, someone will end up being able to open it. Rosenstein, in a matter of a few sentences, was able to jump from rattling off dire warnings and statistics about cybercrime to suggesting a great way to make cybercrime a lot worse.
Even when Apple said most recently that it “offered assistance and said we would expedite our response to any legal process they send us”, it was only referring to offering training and technical assistance. It wasn’t saying that it could crack the phone’s encryption. Apple’s official position is that it builds products so that the user is the only one with the key. The fact that the FBI was able to pay some hackers $US900,000 ($1,171,387) to unlock the San Bernardino shooter’s phone means that Apple has not done a bulletproof job at building that encryption. But still, as far as we know, the goal is real – to build a phone without backdoors because that’s the safest way to do it.
Rosenstein and his colleagues act as if companies such as Apple are protecting criminals, and dodging legal warrants. In fact, companies such as Apple are protecting Rosenstein and his colleagues, because they most certainly use technology every day. Warrants don’t apply here because the tech is designed so that no one can be ordered to open it up. Before smartphones and laptops existed, FBI agents weren’t demanding that a neurologist autopsy a dead suspect’s brain to try and find some phone numbers of people they were in contact with. If there was a phone book in the suspect’s house, a warrant allowed them to find it. That hasn’t changed today. Law enforcement needs to start thinking of a locked and encrypted phone as a dead brain. If they can hire some Frankenstein hacker to bring it back to life, fine. But otherwise, just do the police work the old-fashioned way.
If the past few days are any indication, this could turn into another prolonged war of words. Rosenstein and the FBI probably see a political opportunity with public and political sentiment turning against the tech world. Tech needs to do a lot of things better, but one of those things is making encryption more impervious to the FBI.