Over the weekend, a user on Twitter pointed out that two of Showtime’s websites had a script running in the background that’s used to hijack visitors’ CPUs to mine cryptocurrency. Other users and outlets later confirmed that the code was present. Now it’s gone, and Showtime refuses to answer questions.
Image Source: Twin Peaks/Showtime
[referenced url=”https://gizmodo.com.au/2017/09/how-to-stop-pirate-bay-and-other-sites-from-hijacking-your-cpu-to-mine-cryptocoins/” thumb=”https://i.kinja-img.com/gawker-media/image/upload/t_ku-large/bgaacr2efjb2aloxc4vo.jpg” title=”How To Stop Pirate Bay And Other Sites From Hijacking Your CPU To Mine Cryptocoins” excerpt=”This past weekend, the popular torrenting site The Pirate Bay caught some flak for testing out a new system that used visitors’ CPU power to generate cryptocurrency profits for itself. This tactic has been around for years, but the high profile implementation signals that it’s probably time to start blocking this crap. Here’s how it’s done.”]
Cryptocurrency miners have been in the news recently because The Pirate Bay caught some flak about a week ago for testing out a new service called Coinhive without informing users. The Coinhive miner uses the website visitors’ extra CPU power to generate a cryptocurrency called Monero (it’s like bitcoin but more private). This isn’t necessarily a nefarious thing to do. Coinhive is trying to present itself as a novel and legitimate way for websites to make some money from visitors. The company takes 30 per cent of the Monero that’s mined by users’ CPUs and the website keeps the rest. It could be a nice way to avoid advertising — but it’s not cool to do this without getting users’ permission.
On Monday, the security-focused website Bleeping Computer posted this screenshot of showtimeanytime.com’s site code indicating the presence of Coinhive’s miner:
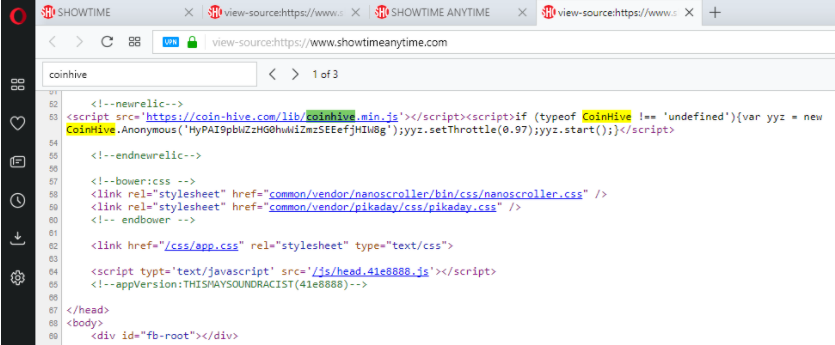
Screenshot: Bleeping Computer
That highlighted script is what a website would need include if it wanted to use Coinhive’s services. Multiple outlets, including The Register, found that the script was present in both Showtime’s home site showtime.com as well as showtimeanytime.com, its official streaming site. When we reviewed the source code, it appeared that the script had been removed but not its comment container marked “newrelic”:
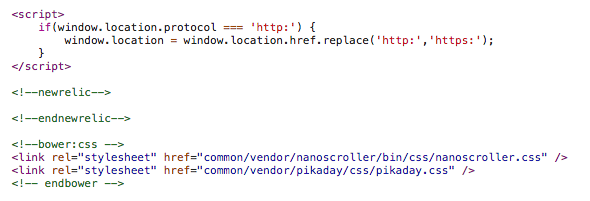
Screenshot: Gizmodo
We reached out to Showtime earlier this afternoon to ask if this script was included intentionally or if an outside actor had perhaps hacked its website. After multiple attempts to get an answer, a spokesperson for Showtime bluntly replied, “We decline comment.”
If Showtime intentionally included the script, it would be a less worrisome situation. As we said, this code isn’t necessarily bad, it just takes up some of your processing power. But even though Coinhive is just a couple of weeks old, researchers have found that malware developers have quickly begun to add it to their toolbox of scams. Coinhive doesn’t endorse that kind of usage and has explicitly voiced its disapproval for using its service without notifying users.
The comment around the script in the code refers to New Relic, which is also the name of a web analytics firm. We reached out to the firm to ask if they had any knowledge about the situation. A spokesperson declined to confirm what relationship New Relic has with Showtime, but denied the code was inserted by one of their workers:
We take the security of our Browser Agent extremely seriously and have multiple controls in place to detect malicious or unauthorised modification of its script at various points along its development and deployment pipeline. Upon reviewing our products and code, the HTML comments shown in the screenshot that are referencing newrelic were not injected by New Relic’s agents. It appears they were added to the website by its developers. Given that this block was not injected by the New Relic agent, we have nothing further to comment.
In the end, we don’t really know what’s happening here. Both Showtime and New Relic don’t want to talk about it.
Until Showtime decides to explain what’s going on, you can read about how to block cryptominers right here.
