A trove of more than 560 million login credentials has been exposed by a leaky database, researchers revealed on Tuesday, including email addresses and passwords stolen from as many as 10 popular online services.
The dataset, which remains insecure, was first discovered this month by the Kromtech Security Center. It was further verified by Troy Hunt, a noted security researcher and the creator of “Have I Been Pwned“, a service that helps users determine whether their accounts have been compromised.
Kromtech researcher Bob Diachenko told Gizmodo on Tuesday that the leaky database contains roughly 243.6 million unique email addresses, an overwhelming majority of which were compromised during previous (and since secured) data breaches at LinkedIn, DropBox, LastFM, MySpace, Adobe, Neopets and Tumblr, among others.
The identity of the individual who amassed this database is not presently known, though the researchers have taken to calling them “Eddie” after a user profile discovered on the storage device.
Kromtech stumbled upon the insecure device, which remains active and unprotected by a password, during a routine security audit with Shodan, a search engine that scans internet-connected devices for open ports and databases.
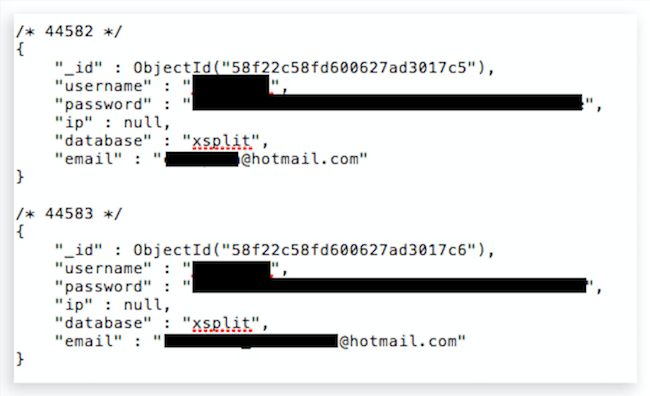
This snippet from Eddie’s database comes from the XSplit dataset. (XSplit was hacked in November 2013, leaking some 2.9 million usernames, email addresses and passwords in md5 hash.)
According to Diachenko, the device is running an insecure version of the open-source database program MongoDB, early versions of which are notoriously easy to misconfigure. The default settings in these early versions of the program allow anyone with know-how to remotely browse database contents. Later versions address the vulnerability, but many people are slow to update the software.
Overall, the Kromtech audit revealed as many as 313 large MongoDB databases containing “several terabytes of data hosted in the US, Canada, and Australia” which may be susceptible to theft — though some may be been intentionally accessible to the public.
Kromtech typically waits until a breach is secured before announcing its discovery. In this case, however, the credentials all originate from previously disclosed breaches.
[referenced url=”https://gizmodo.com.au/2017/05/huge-trove-of-confidential-us-medical-records-discovered-on-unsecured-server-accessible-to-anyone/” thumb=”https://i.kinja-img.com/gawker-media/image/upload/t_ku-large/zp0lgndtufjjtzfntd7k.jpg” title=”Huge Trove Of Confidential US Medical Records Discovered On Unsecured Server Accessible To Anyone” excerpt=”At least tens of thousands, if not millions of medical records of New York patients were until recently readily accessible online to just about anyone who knew how to look.”]
“We wanted once again to highlight the importance of changing the passwords, because more and more malicious actors seem to exploit the data grabbed from previous leaks and hacks,” Diachenko said.
After reviewing a sample set of 10,000 credentials, Hunt determined that up 98 per cent of the passwords and email addresses may already be contained on the “Have I Been Pwned” website. (Hunt’s website allows users to see if their accounts have been compromised, but it does not display stolen passwords, unlike the database Kromtech found.)
“That’s astronomically higher than what I’d seen after loading a typical breach (usually 50 to 60 per cent),” said Hunt, “and as Bob and I discussed, a very large proportion of them have come from existing incidents.”
The database compiled by “Eddie” — among others recently loaded into Hunt’s website — show that attackers are “weaponising large collections of credentials from a wide variety of sources,” he said.
The lesson here is simple: Today is a good day to change your passwords. And if you haven’t already, get yourself a good password manager.
