Federal authorities from around the world have finally shut down “Avalanche”, a massive network of 500,000 hijacked machines that hackers used to launch malware and phishing attacks. In fact, at one time, the Avalanche network was responsible for two-thirds of all global phishing attacks.
Image: Flickr / Simon Desmarais
As part of this unprecedented sting operation carried out by Europol and the US Federal Bureau of Investigation, five people were arrested, 37 locations were searched and 39 servers were sized, according to Europol. The European law enforcement agency says that another 221 servers were taken down after abuse notifications were sent to the server’s hosts, and that 800,000 domains have been blocked. Avalanche hosted more than “two dozen of the world’s most pernicious types of malware and several money laundering campaigns,” according to the FBI.
“The Avalanche network was used as a delivery platform to launch and manage mass global malware attacks and money mule recruiting campaigns,” Europol wrote in a statement.
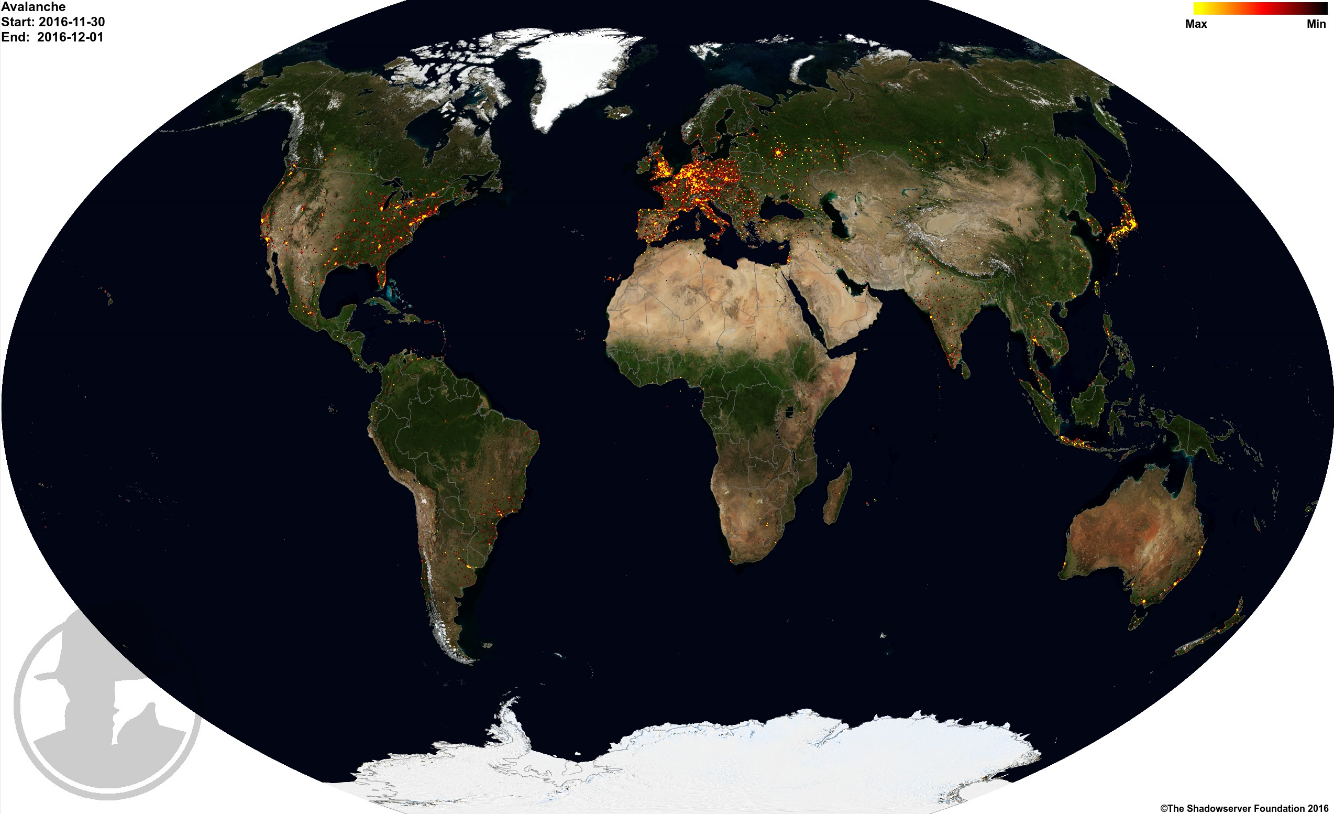
Each red dot represents a sever in the Avalanche network. Source: shadowserver.org via Brian Krebs
The FBI confirmed that Avalanche helped hackers steal absurd amounts of money. The agency explains, “The monetary losses associated with malware attacks conducted over the Avalanche network are estimated to be in the hundreds of millions of dollars worldwide, although exact calculations are difficult due to the high number of malware families present on the network.”
Avalanche’s scale is what makes this so unprecedented. According to Europol, there are victims of malware sent out affected people in 180 countries. That’s almost all of the countries in the world. On top of that, Avalanche sent a million emails with “damaging attachments or links” every week.
It took four years for authorities to finally bust Avalanche. Their investigation was triggered when ransomeware sent from Avalanche infected computers in Germany. Europol explains:
Millions of private and business computer systems were also infected with malware, enabling the criminals operating the network to harvest bank and email passwords. With this information, the criminals were able to perform bank transfers from the victims’ accounts. The proceeds were then redirected to the criminals through a similar double fast flux infrastructure, which was specifically created to secure the proceeds of the criminal activity.
Europol cites a technique called “double fast flux”, as primary reason Avalanche operators were able to get away with their scheme for so long. It might sound like time travelling, but double fast flux is a technique used to evade detection that quickly moves a domain name to point to a different server. “The complex setup of the Avalanche network was popular amongst cybercriminals, because of the double fast flux technique offering enhanced resilience to takedowns and law enforcement action,” Europol wrote.
Now that Avalanche is gone, it’s only a matter of time until another massive botnet springs up to replace it.
[Brian Krebs via Europol]
