As Apple had its annual celebration of its own awesomeness, I tuned in to see how Apple’s new operating system will provide better security and privacy to its users.
Apple “cares about privacy”
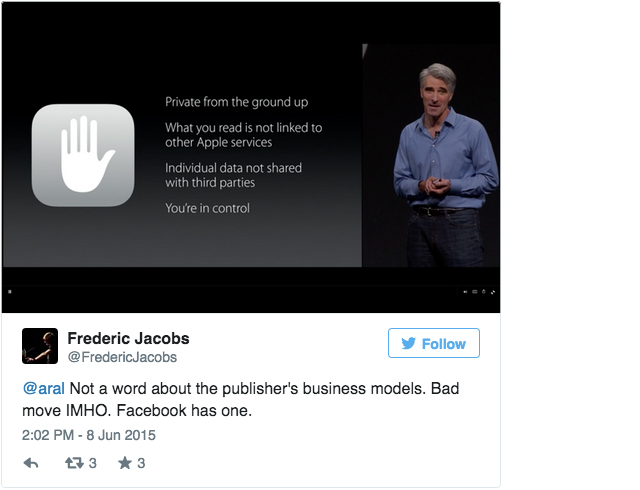
During the Keynote, Craig Federighi has made it really clear that Apple “seriously don’t want to know [your personal information]”. This has been a theme in Apple’s statements, a good differentiator from Android, that sucks more and more user’s data directly to Google servers.
https://twitter.com/FredericJacobs/status/607967114209726465
Apple also announced a “News” app that would aggregate newsfeeds. Again, making claims about strong privacy.
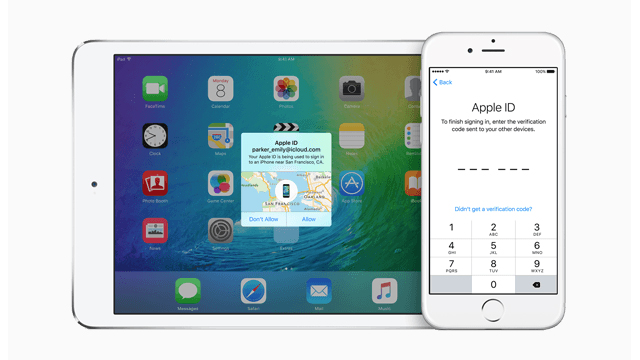
iCloud 2FA
iOS 9 has a new interface for iCloud two-factor authentication.

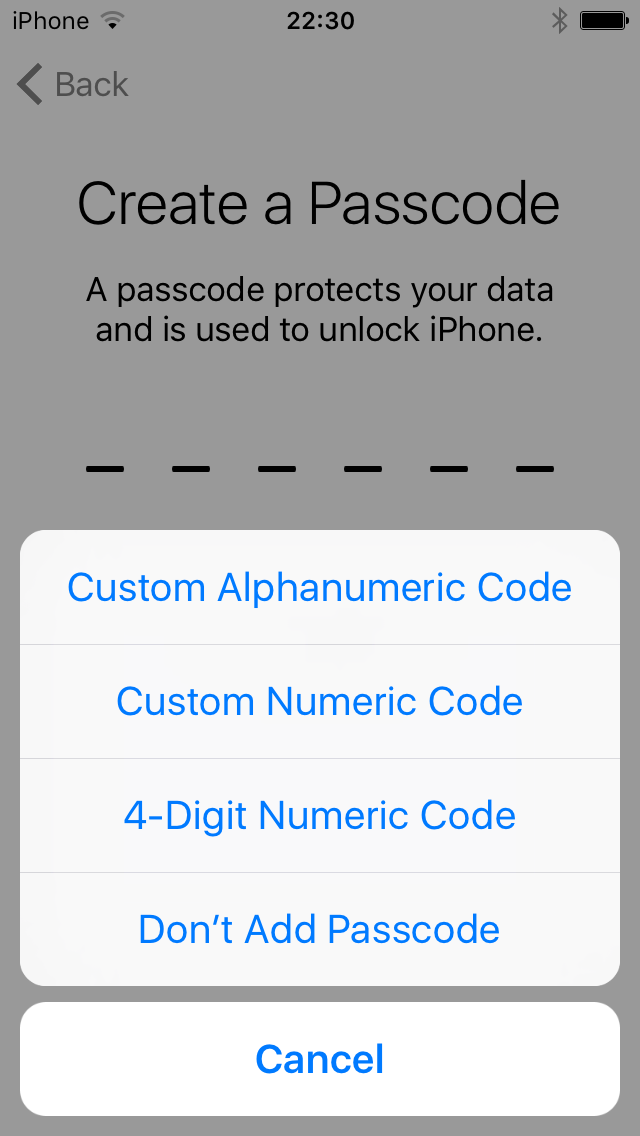
New password requirements
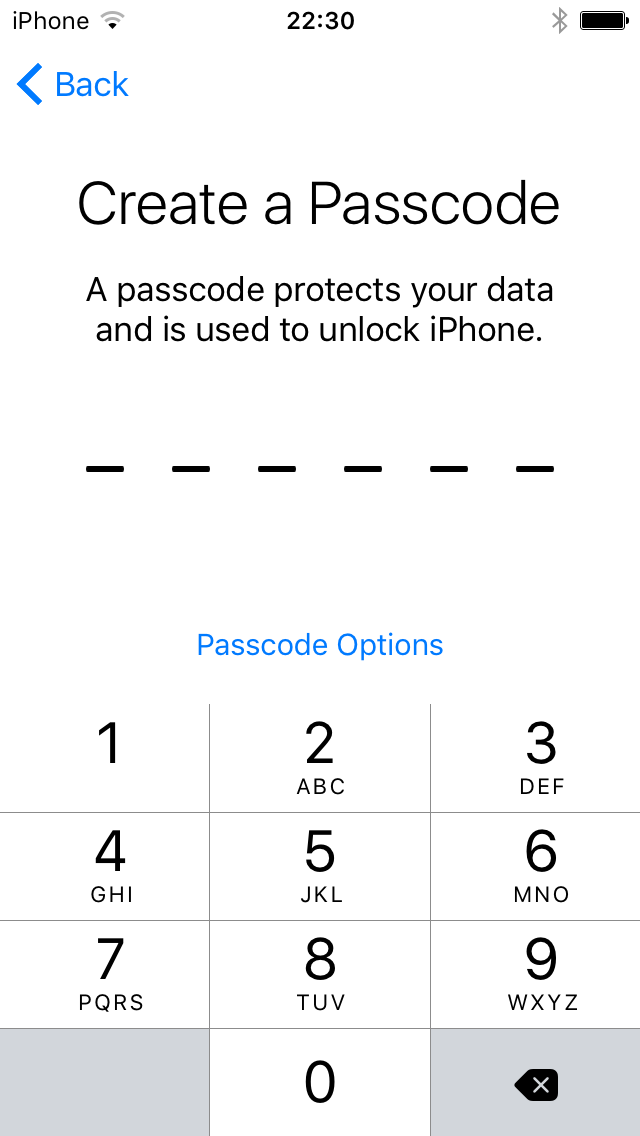
First thing that struck me as I booted my iOS 9 iPhone was that the new default password format — 6-digit passcodes. Up from 4-digits previously. I don’t claim that this is a significant security improvement, it’s not for an attacker that can mount an offline bruteforce attack on your phone. But it’s an strong signal, months after the FBI complained about Apple’s default encryption in iOS 8. Notice that Apple does not let you continue without making a 6-digit password or selecting another passcode option.
VPN API = Tor on iOS?!
It was previously not possible to proxy traffic over a protocol that was in the supported VPN list. This is now changing with Apple opening up a VPN extension API. Some companies, such as OpenVPN has been given beta-access to a network proxying API but it was not a documented or authorised API for third-party developers.
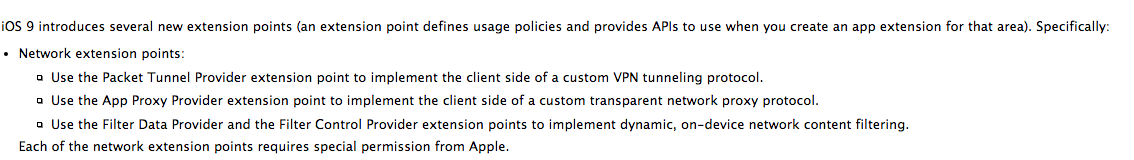
These networks allow way more than simply tunnelling the device’s traffic into a VPN service or Tor. It enables a whole new category of apps that prevent trackers too. You can for instance filter all traffic going to known analytics/advertising networks! Advanced adblocking/Disconnect for iOS on the way?
https://twitter.com/FredericJacobs/status/607995091114983424
You can read more about these APIs in the release notes.
SSL updates
LibreSSL: OS X 10.11 ships with LibreSSL.
Safari Cipher Suites: Goodbye SSLv3!
‘HSTS’ for Apps: You can package your iOS in such a way that all the connections will go over HTTPS, enforced by the OS.
https://twitter.com/FredericJacobs/status/607994422379343873
App Transport security is not only about forcing HTTPS but Platform State of the Union Address claims that it enforces “Best Practice” HTTPS which according to Apple’s standards mean: TLS 1.2 and PFS cipher suites. Apple claims it will not downgrade to previous versions of TLS and non-PFS ciphers and that their standards will evolve over time.

To benefit of these “hardened” connections, developers need to use Apple’s Foundation framework’s NSURLSession on both iOS9 and OS X 10.11. It is possible to opt-out for now, “while deploying server-side support.”
Certificate Transparency: The SecureTransport documentation has not been updated yet but there does appear to be support for Certificate Transparency, which is really exciting!
From the header, it seems that the SSLSetEncryptionCertificate method has been modified. But unsure what has been changed yet. Maybe related to the exportable suites they mentioned in the previous specification?
SSL servers that enforce the SSL3 or TLS1 specification to the letter do not accept encryption certificates with key sizes larger than 512 bits for exportable ciphers (that is, for SSL sessions with 40-bit session keys). Therefore, if you wish to support exportable ciphers and your certificate has a key larger than 512 bits, you must specify a separate encryption certificate. [Source]
Unfortunately the updates in SecureTransport code have not been open-sourced and probably won’t before release.
Safari
Safari also got some security updates.
Extensions signed and hosted by Apple: All extensions in the Safari Extensions Gallery are now hosted and signed by Apple. Users can trust that the Safari Extension they install is the one you submitted.
Apple says that developers can still sign and distribute extensions that are signed with developer certificates but these won’t auto-update.
Content-blocking: The new Safari release brings Content Blocking Safari Extensions to iOS. Content Blocking gives your extensions a fast and efficient way to block cookies, images, resources, pop-ups, and other content.
Potentially a big deal for adblocking software developers. Users have been complaining about how much memory and CPU Adblock was using, resulting in delayed page loading. This API is available as an App extension on iOS and Safari extension on OS X.
More information about Safari related changes.
Code-signing
Apple also has surprised everyone by dropping the necessity of joining the paid $US99 iOS developer program to run applications on devices. Comex raises the interesting point that this could be used as a future injection point for jailbreaks (as stolen Enterprise certificates were used in the past).
Bitcode
To make apps smaller, Apple has decided to make you upload some intermediate representation (LLVMR IR?!) to iTunes Connect and Apple would then be compiled without needing to re-submit. I’m really wondering how this plays out with code signing. I believe only Apple would be in the capacity to sign the final binary. Goodbye the remote possibility (Apple’s FairPlay DRM encryption made it difficult already) of having reproducible builds on iOS.
Here is the (scary) future of native apps for iOS and watchOS. They will be compiled and linked by Apple. pic.twitter.com/r6hiW2ZNL4
— Andrey Belenko (@abelenko) June 8, 2015
More about Bitcode and App Thinning.
Writing safer Objective-C
Objective-C has also gotten some love this year. Apple introduced generics for Objective-C, this is really cool (and overdue). More typesafety FTW!
Swift
Swift is a great memory-safe language without garbage collection. And Apple announced they open-sourced it and will provide a standard library for iOS/OS X and Linux. This is terrific news.
Swift and Rust are two emerging languages for cryptographic implementations. Swift’s memory management model (ARC) does seem more intuitive to me that Rust’s borrowing model, but I guess you get used to it.
Rootless?
9to5mac had reported that iOS9 would be “rootless” but that does not seem to be the case in the betas.
It is the case however that Apple changed privileges of Admin users on OS X 10.11.
Admins are no more able to have access to kernel-level features. This is great for most users since this will prevent some kinds of advanced malware persistence on the Mac.
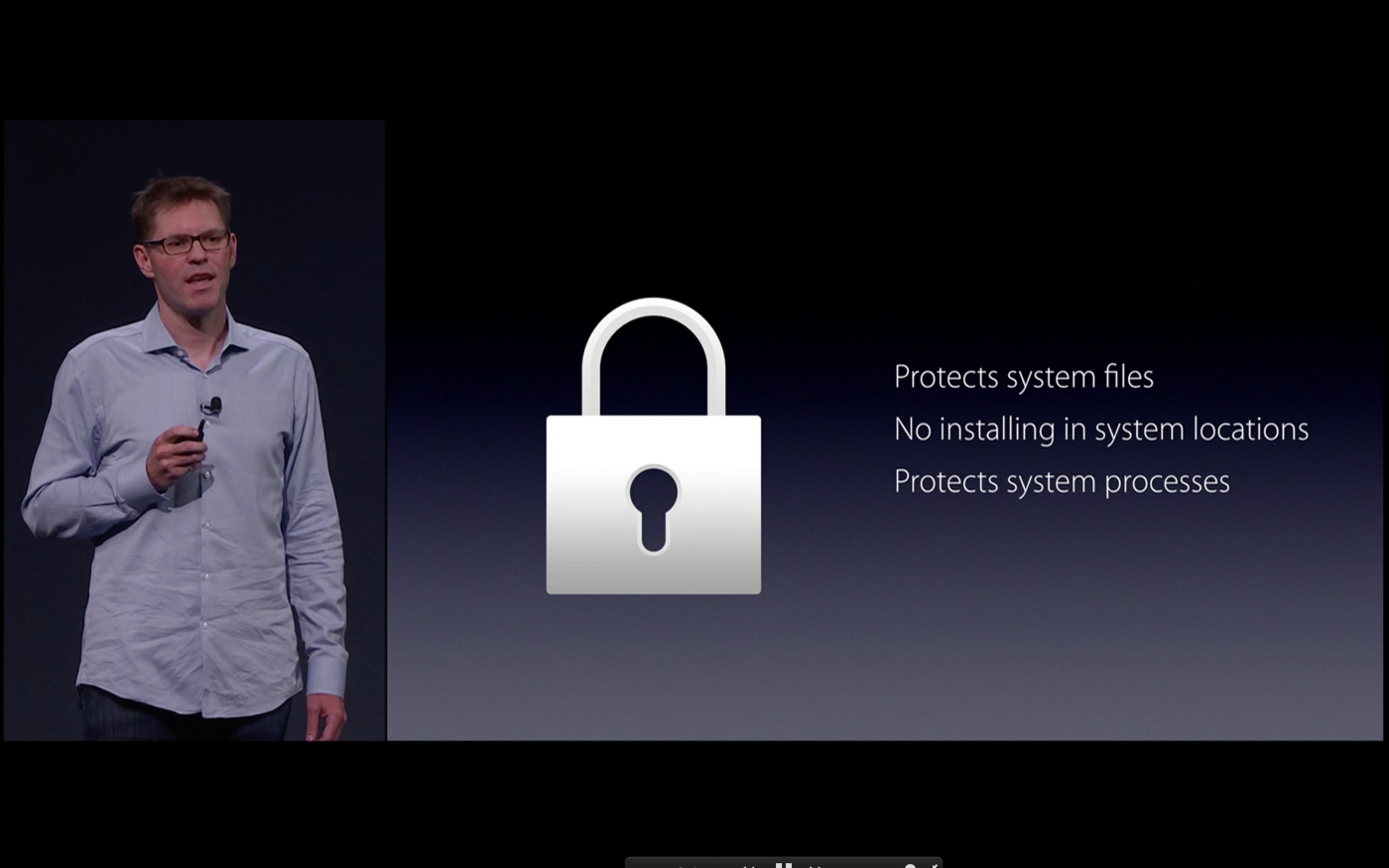
For those of us requiring to be able to write Kernel modules, Apple has a special kit that allows you to “jailbreak” your Mac to get kernel-level access.
Updates coming
WWDC is only starting, this post will be updated as documentation comes in and more detailed sessions are given on this tech. If you have found something in the documentation that deserves to be featured here, please tweet at me or drop me a line.
Frederic Jacobs is a security researcher.
This post originally appeared on Medium. It has been republished under a Creative Commons licence.