Researchers at the University of Washington in Seattle have just hijacked a teleoperated surgical robot, demonstrating major security weaknesses in the machines that may eventually replace a surgeon’s hands in hospitals worldwide. Yikes.
When trained surgeons are a plane ride away, remotely operated surgical bots can save lives.
Doctors have been performing telesurgical procedures since 2001, when a surgeon in New York successfully removed the gall bladder of a patient in France. While telesurgery is by no means the status quo yet, it may well be in the future, given that the medical industry is quickly embracing robots in many aspects of patient care.
The advantages of remote surgery may be obvious, but like any tool that relies on the telecommunications, there are inherent security risks. Communication between the surgeon and the robot typically takes place over public networks, and in some cases, poor internet connections. To explore how cyberattacks could disrupt a surgical robot, security researchers used the Raven II, a medical bot with two surgical arms that are manipulated through a state-of-the-art control console that includes a video feed and haptic feedback. The researchers controlled the robot over a standard network connection, using it to move rubber blocks from one part of a peg board to another.
MIT Tech Review describes the researchers’ experiments:
The team tries out three type of attacks. The first changes the commands sent by the operator to the robot by deleting, delaying or re-ordering them. This causes the robot’s movement to become jerky and difficult to control.
The second type of attack modifies the intention of signals from the operator to the robot by changing, say, the distance an arm should move or the degree it should rotate and so on. “Most of these attacks had a noticeable impact on the Raven immediately upon launch,” say Bonaci and co.
The final category of attack is a hijacking that completely takes over the robot. This turns out to be relatively easy since the Interoperable Telesurgery Protocol is publicly available. “We effectively took control over the teleoperated procedure,” they say.
They even worked out how to generate movements that triggered an automatic stop mechanism built in to the robot….By constantly sending commands that triggered this mechanism, the team were able to carry out a kind of denial of service attack. “We are able to easily stop the robot from ever being properly reset, thus effectively making a surgical procedure impossible,” they say.
So yea, that all sounds pretty bad. As a final coup de grâce, the researchers note that the robot’s video connection was publicly accessible, meaning basically anyone could watch the operation in real time.
Many types of cyberattacks could be prevented by encrypting communications between the control console and the robot. But as we’re all well aware, crafty hackers can sometimes find ways around even the most sophisticated security systems. It’d seem that medical practitioners, policy makers and the public have to make some tough choices about what level of telesurgery security is acceptable. And if we’d like to avoid a Saw-esque horror scene, this is probably a conversation we ought to have sooner rather than later.
Read a pre-print of the study on arXiv.
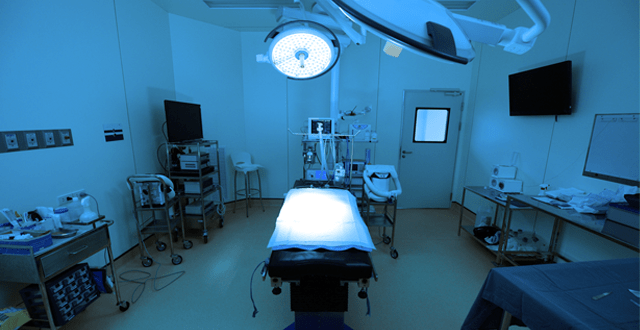
Top image: A da Vinci surgical system, via Wikimedia