A good Bitcoin mining rig is hard to find. They’re expensive, they take up space, they wrack up huge energy bills. Not at all practical for your average ESEA gaming network employee. Nefarious code that turns 14,000 of your users into an unwitting personal bitcoin botnet? Totally doable.
Like so many great schemes, it must have seemed perfect at the start, like Richard Pryor pulling half cents out of thin air in Superman III. ESEA is one of the largest competitive gaming leagues in North America, if not the world, with cash prizes approaching $US100,000 each season. Its users are an elite breed, who use elite graphics cards — the kinds that can slowly, surely, reliably churn out Bitcoins if given a gentle nudge in the right direction. Or in this case, were marched there at gunpoint.
The best/worst part? The as-yet-unnamed rogue employee didn’t even have to come up with come up with any clever code himself. ESEA did that bit for him.
The Trojan Mine
Recently, ESEA decided to experiment with Bitcoin mining. Specifically, with building the feature into its product so that its users could, if they wanted to, harness their powerful GPUs for digital cash instead of digital kills. The company got deep enough into the testing phase that, according to an ESEA news release, ESEA even had it up and running on two of its administrators’ rigs. And then, on April 13, it pulled the plug.
Or at least, they thought they did.
As the release goes on to describe, one of the employees involved in the test decided that the code was too good to just abandon. In fact, it could be incredibly useful if you were enterprising enough — and immoral enough — to figure out how to deploy to the rigs of 14,000 of your network’s most valued members. Just hide it somewhere that they need but would never question. Somewhere like, say, ESEA’s anti-cheat client, the pride of the company.
And that’s where it hid, until a user — not ESEA — found out what was going on. Yesterday.
Quitting Time
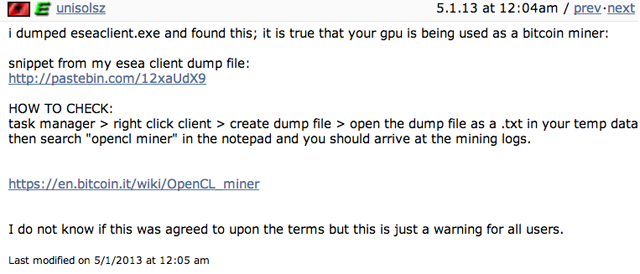
At just after midnight yesterday, ESEA user unisolsz discovered that his GPU was being used for something other than, well, anything he intended. Specifically, that it was mining Bitcoins. He sent out a warning in the ESEA forums, and the company pulled the plug.
In just those two weeks though, the damage was done. The employee had racked up close to BTC30, which is $US3713.55 in dollars today (and either twice or half that tomorrow, given the viscosity of Bitcoin).
To help make things right, ESEA is donating twice that amount to the American Cancer society, and — since it’s still unsure exactly which users were affected, and how many, and to what degree — increasing the prize pot by that much, as well. It’s also offering free memberships to people who claim their graphics cards were damaged by being turned into digital drills.
Ultimately, it’s not so much a victimless crime as an unquantifiable; it’s not like the people affected lost money they already had, or were going to be mining their own Bitcoins anytime soon. But having your GPU manhandled remotely, and being indentured into botnet; these are wrongs that don’t have a price attached to them, other than the anxiety of knowing how easy it was to be compromised. [ESEA, Kotaku, Wired]
