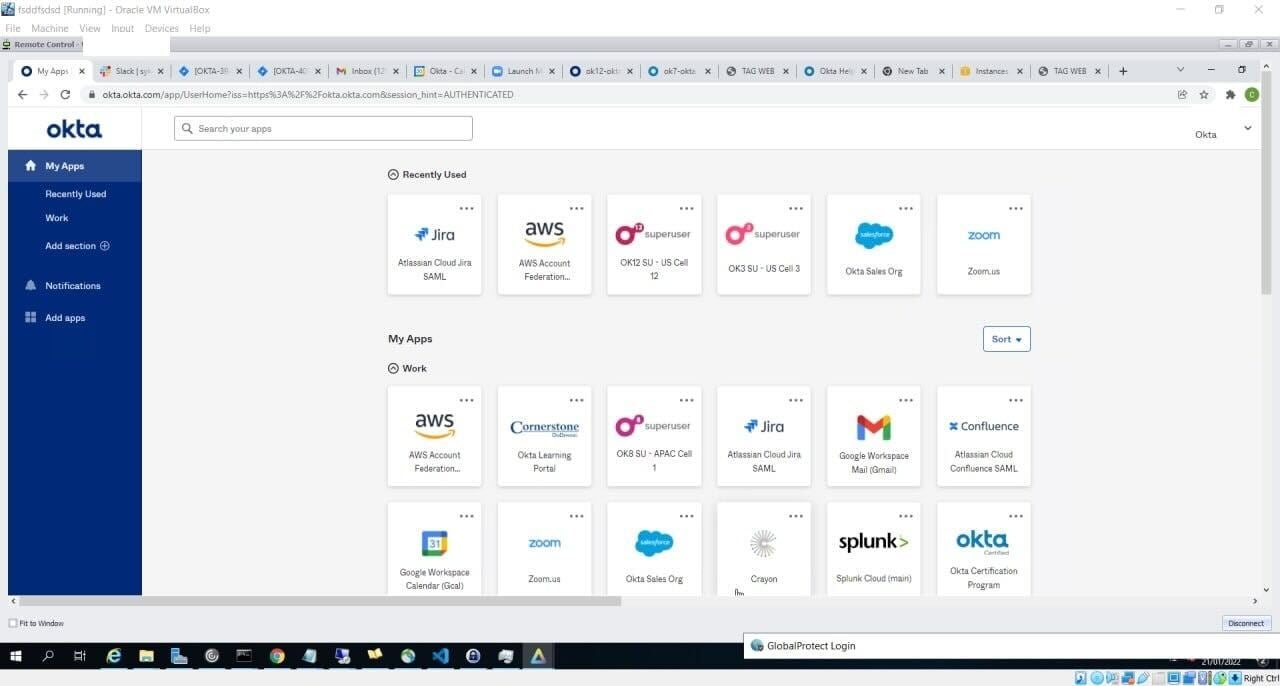
Hacker group LAPSUS$ posted images on its Telegram channel overnight claiming it achieved administrator access to Okta, a user authentication and data management company. And if that’s true, it’s potentially bad for a number of large firms that use Okta services.
“Just some photos from our access to Okta.com Superuser/Admin and various other systems,” the hacking group wrote on Telegram.
“For a service that powers authentication systems to many of the largest corporations (and FEDRAMP approved) I think these security measures are pretty poor.”
The hacker group went on to post in all caps explaining that they didn’t access or steal any databases from Okta. “Our focus was ONLY on Okta customers,” the hacker group explained.
If the screenshots are accurate they include a timestamp from January of this year, suggesting the hackers have potentially had access for months. It’s unclear whether the hackers still have access to Okta systems. But for its part, Okta claims the hackers only had limited access through a subcontractor.
“In late January 2022, Okta detected an attempt to compromise the account of a third party customer support engineer working for one of our subprocessors,” a spokesperson for Okta, Chris Hollis, said in an email to Gizmodo early Tuesday.
“The matter was investigated and contained by the subprocessor. We believe the screenshots shared online are connected to this January event. Based on our investigation to date, there is no evidence of ongoing malicious activity beyond the activity detected in January.”
The hack, first reported by Reuters, comes after LAPSUS$ claimed on Monday it had gotten 37 GB worth of source code for Microsoft’s Bing search engine and the Cortana virtual assistant.
LAPSUS$ previously hacked tech companies like Nvidia, Ubisoft, and Samsung, typically working under a data extortion model, as Bleeping Computer notes. The hacking group will acquire large amounts of sensitive data and demand money in order to get a big payout from the company that was hacked. If the sum isn’t paid, the hacking group leaks the data publicly.
In a more typical ransomware situation, the data is encrypted and people on the inside can’t get access to their own information anymore, but as Wired points out, LAPSUS$ doesn’t bother with locking up any data. The group just steals it outright, which is very unusual.
LAPSUS$ hasn’t made any demands known to be related to the Okta hack. At least not yet.
