For close to two years, the FBI clandestinely operated an encrypted communications platform called “Anom” that was used almost exclusively by drug traffickers and organised crime, a recently unsealed federal affidavit claims.
The chat app appeared to offer criminals a private, secure means of communication while they engaged in their illicit dealings. In reality, the FBI had developed a confidential relationship with the product’s developer and was using the app as a direct backdoor into their shadowy networks, court documents allege.
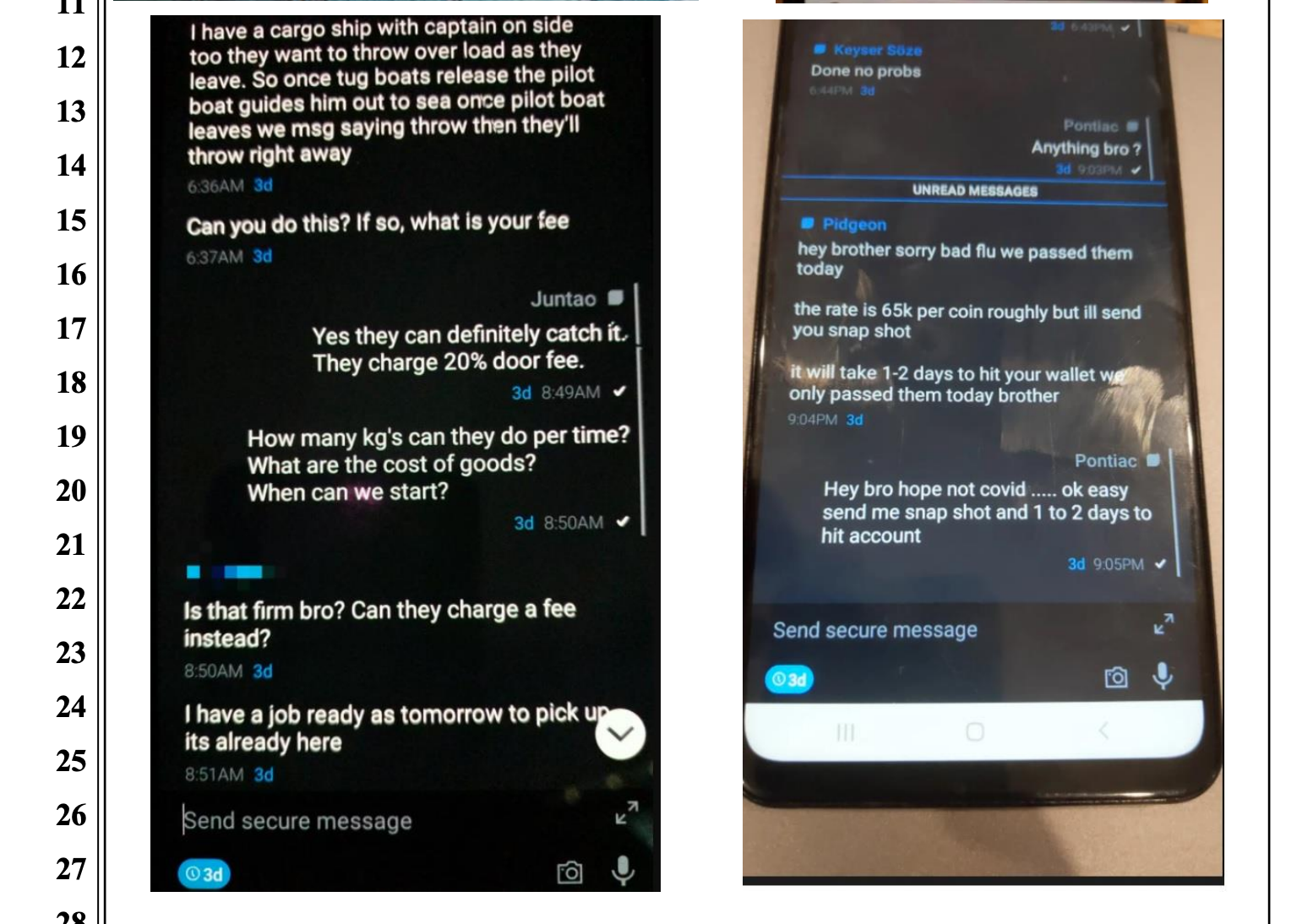
Altogether, Anom allowed agents to monitor 11,800 devices in 90 countries — the likes of which involved activity by as many as 300 distinct transnational crime organisations. Such groups included “Italian organised crime, Outlaw Motorcycle Gangs, and various international narcotics source, transportation, and distribution cells.” In total, authorities claim to have collected over 20 million messages and more than 450,000 photos from the encrypted platform, many of which appear to detail the sophisticated supply chains and business practices of transnational drug traffickers. The federal affidavit with this information was initially shared with Gizmodo by professional researcher and academic Seamus Hughes.
This whole operation is part of a globally coordinated law enforcement action involving multiple governments, dubbed “Trojan Shield.” A sort of gargantuan honeypot, “Trojan” involves not just the FBI, but also the Australian Federal Police (AFP), Europol, and other authorities in the countries where the criminals were active. So far, the investigation has led to charges for “more than one hundred organised crime members,” AFP announced Tuesday, adding that the “encrypted communications” smashed by police apparently involved “plots to kill, mass drug trafficking, and gun distribution.”
As a law enforcement investigation, “Trojan” represents a virtually unheard-of effort by authorities to monitor the communications of alleged crime syndicates via infiltration of the dark side of the encrypted communications industry.
The FBI was initially able to hijack the Anom platform by compromising a high-level criminal who was involved in developing products for the encrypted communications industry, court documents state. The relationship with the source began in 2018, not long after the FBI had conducted an investigation into Phantom Secure, an encrypted phone company that was found to be selling its products “exclusively to members of criminal organisations.”
At the time, the confidential informant was involved in developing “the “next generation” encrypted communications product, poised to compete for market share against established hardened encrypted device competitors,” documents state. The source had also “previously distributed both Phantom Secure and Sky Global devices to TCOs [transnational crime organisations] and had invested a substantial amount of money into the development of a new hardened encrypted device.” Subsequently, the informant “offered this next generation device, named ‘Anom,’ to the FBI to use in ongoing and new investigations. The CHS also agreed to offer to distribute Anom devices to some of the CHS’s existing network of distributors of encrypted communications devices, all of whom have direct links to TCOs.”

The documents reveal not just a shrewd, massive law enforcement operation, but also the sophisticated, high-tech nature of international criminal activity today. The past several years have seen numerous similar policing actions aimed at encrypted platforms that cater to criminals. The increasing accessibility of these products has naturally led to their use in corruption. Most recently, police dismantled Sky Global, whose CEO is accused of supplying encryption technology to international drug cartels. At the same time, prosecutions and investigations are ongoing into the alleged criminal networks that used EncroChat, another encrypted platform that police infiltrated last summer.
“The Trojan Shield investigation has unveiled how criminal organisations compartmentalise their activities with multiple brands of hardened encrypted devices. For example, some users assign different types of devices to different parts of a drug trafficking transaction,” the federal affidavit states. “For example, I have seen conversations where Anom is used for the logistics of the drug shipments, but Ciphr or Sky were used to coordinate the concealment of the illicit proceeds.”
“A goal of the Trojan Shield investigation is to shake the confidence in this entire industry because the FBI is willing and able to enter this space and monitor messages,” the document says.
