A startup in Iran recently suffered a large data breach in which millions of its user records were exposed to the internet and then subsequently destroyed by a cyberattack involving a bot. The disruption appears to be part of an ongoing trend in which bad actors surf the web looking for insecure databases, then pounce on them to steal or destroy the data.
Raychat, which was founded in 2017, has sought to make a name for itself as a business and social messaging application. It partners with businesses and websites, which use it for sales and customer service, among other things. It was featured at Iran’s Silk Road Startup Summit several years ago, and a website that rates startups by their social engagement and other metrics lists it as one of Iran’s more popular new companies.
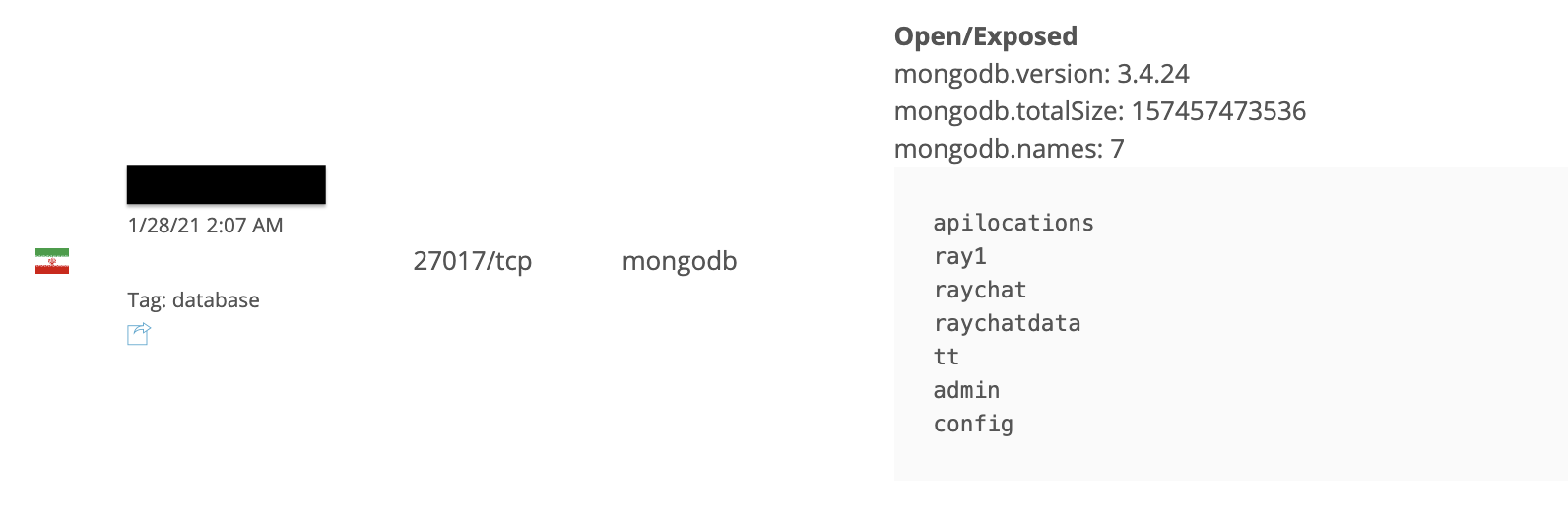
However, until recently, the company was storing its user data on a misconfigured MongoDB database. MongoDB is an NoSQL database, a kind of storage application that, among other things, is frequently used by app companies to handle large volumes of user data. However, when misconfigured, NoSQLs can leave millions of documents vulnerable. In this case, a bad actor was able to essentially walk right in Raychat’s front door, then leverage a bot attack, which the company admits destroyed the database. The breach was discovered by security researcher Bob Diachenko.
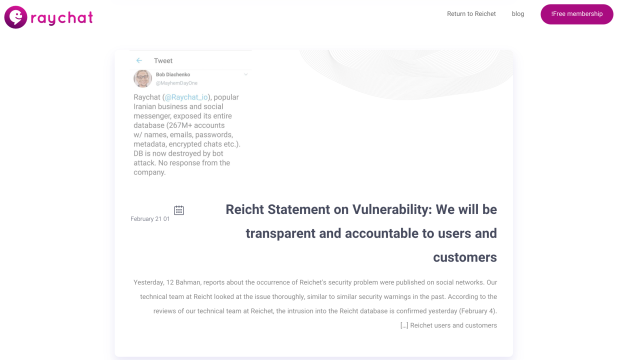
Raychat (@Raychat_io), popular Iranian business and social messenger, exposed its entire database (267M+ accounts w/ names, emails, passwords, metadata, encrypted chats etc.). DB is now destroyed by bot attack. No response from the company. pic.twitter.com/rC4Uvm2U97
— Bob Diachenko (@MayhemDayOne) January 31, 2021
Diachenko said that he came across the vulnerability using publicly accessible open-source search tools, like Shodan, which is used to search for devices connected to the internet. A lot of NoSQL databases like Mongo are targets “for bot attacks operated by malicious actors who scan the internet for open and unprotected dbs [databases] and wipe their contents, with only a ransom note left,” Diachenko said in a Twitter DM. A recent report from Comparitec breaks this down, explaining how botnets are leveraged to scrape and download large data troves before destroying the original:
[Hackers use] …malicious requests that modify and/or destroy the data on the server. In many cases, the data is downloaded by the attacker before being deleted. The attacker then leaves a note demanding ransom for safe return of the data.
In Raychat’s case, Diachenko says a README ransom note popped up, demanding 0.019 in bitcoin (around $919, at current exchange rates). It is possible but unlikely that a majority of the app’s data was downloaded before it was destroyed, he said. In many of these cases, the hacker is not actually “able technically to store all of the amounts they claim to copy,” he said.
Diachenko reached out to the company but says he initially got no response. After the researcher took his findings to Twitter, Raychat quickly admitted to the breach — while also disclosing that it had been the victim of a bot attack. The company published a statement on its website in which it referenced Diachenko’s tweets and also apologised to users for the inconvenience. “So far there is no evidence of information leakage,” it reads. The attack appears to have occurred very shortly after the discovery of the breach.
Co-founder Ghader Sadeghi confirmed in a message that Diachenko had been helpful in assessing the nature of the breach. “We emailed him,” Sadeghi said, noting that the researcher had helped identify the MongoDB misconfiguration. He stressed the company’s remorse to its users and its willingness to improve. The company has stated that its user data is backed up and will be restored shortly. A spokesperson reached via Twitter said they had “no idea” who was behind the attack. Sadeghi said their legal team was looking into it.
ما ایمیلی رو همه کاربران رایچت جهت تغییر پسورد ارسال کردیم. در این ایمیل هیچ لینکی برای تعویض پسورد ارسال نشده. اگر ایمیلی از رایچت دریافت کردین که لینک تعویض پسورد داره، به هیچ وجه روی این کلیک نکنین.#رایچت
— Raychat (@Raychat_io) January 31, 2021
Company personnel also seem worried about potential phishing attempts as, in a tweet on Jan. 31, the company warned: “We sent an email to all Reichet [Raychat] users to change their password. There is no link to change the password in this email. If you receive an email … with a password change link, do not click on it at all.” The company also appears to have recently suffered a different cyberattack, according to tweets made in December.
Iran’s startup ecosystem is in a particularly fragile condition right now. After a brief “boom” between 2012 and 2016, the country’s new companies have gone through a fairly rough time, largely due to U.S. sanctions and the covid-19 pandemic. When you throw cyberattacks into the mix, it’s a particularly noxious situation.