In a new letter to the editor pulled from the prestigious scientific journal Nature, a team of Israeli researchers pose a frankly wild-sounding question: could a computer hack result in a scientist being swindled into creating a piece of genetic code that’s harmful — or potentially toxic — rather than helpful?
The answer seems to be yes, albeit with some pretty weighty caveats. The “end-to-end cyberbiological attack” described above requires some lacklustre cybersecurity chops from both sides of the genetic research supply chain: both the academics who might order genetic materials online, and the labs that might supply those materials back. While this sort of attack hasn’t been seen in the wild yet, the research team behind the letter pointed out that it’s not outside the realm of possibility — especially as more and more genetic research moves into the digital realm.
At the heart of this hypothetical hack is the software that biologists use to “print” strands of DNA from scratch and then assemble them together, a process known as “DNA synthesis.” In recent years, we’ve seen this synthesizing software underpin tons of groundbreaking biomedical research. In the mad dash to create a treatment for Covid-19, for instance, a handful of major pharma companies turned to using man-made strands of DNA as one of the components of their experimental vaccines.
But software — even software that’s used to write strings of biological code — is still software, which means it can still be hacked. Futurists and scientists alike have been sounding that specific alarm for years. And back in 2017, a team of researchers from the University of Washington even demonstrated that it was possible to encode malware directly into one of these synthetic DNA strands, albeit with a lot of trial and error, and the malware only worked because they intentionally borked the software they intended to attack. (And, as Wired wrote though, “the attack was fully translated only about 37 per cent of the time.”)
Both that case and the case described in this new letter are theoretical. But as the Israeli researchers put it, of these cases are theoretical. But as the Israeli team puts it, “the threat is real” — especially as synthetic DNA underlies more and more biomedical research.
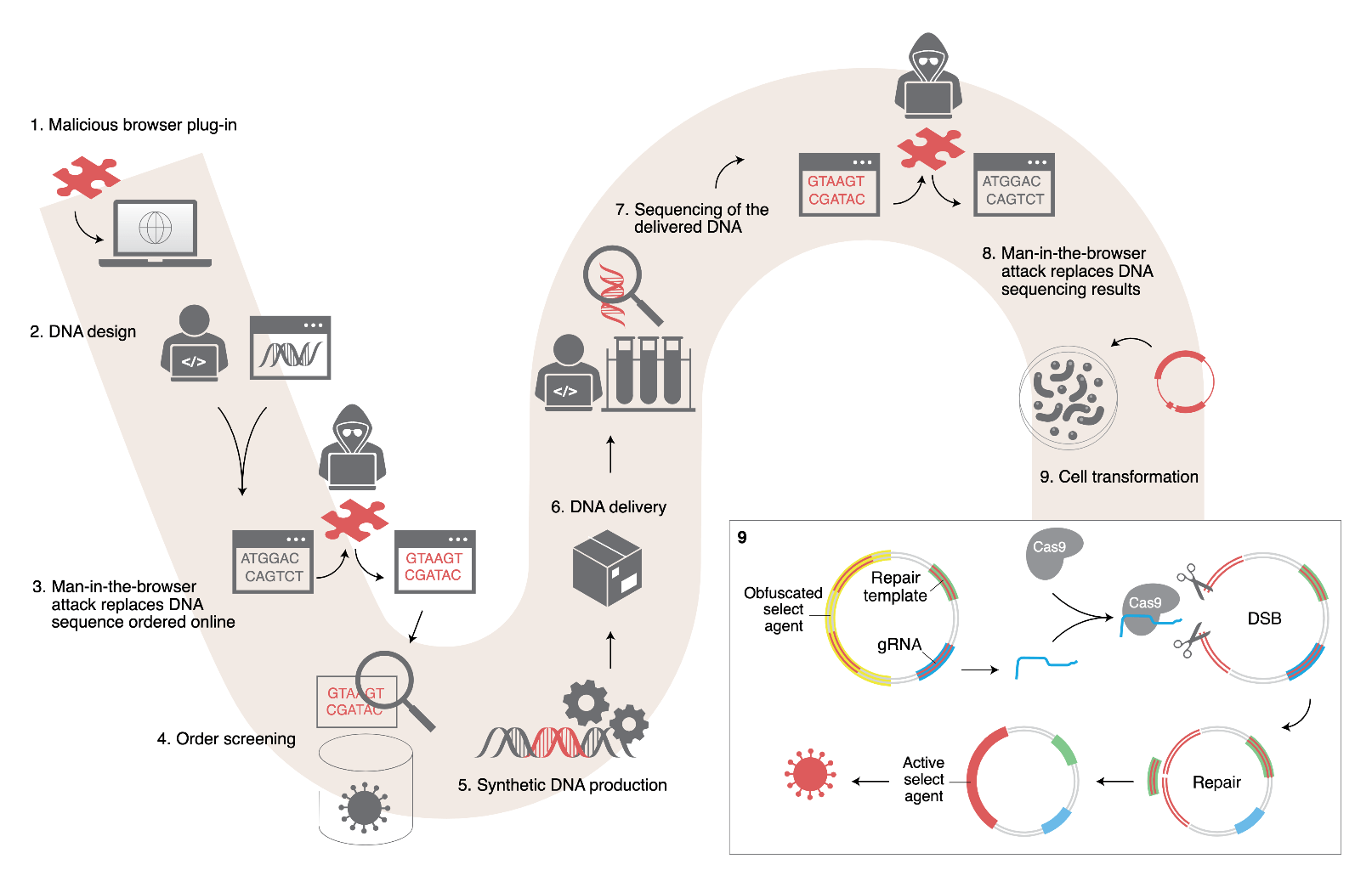
Here’s how the hack would (theoretically) go down: let’s say you have a bioengineer working out of a University, who happens to be working on a new vaccine that requires specific strings of synthetic DNA. These strings are each constructed of four different chemical building blocks — or “bases,” in biology parlance — arranged in a specific sequence.
As the researchers point out, not every academic institution has the greatest cybersecurity chops, which means it’s entirely possible for a bad actor to hijack this engineer’s computer with some sort of malware. Because the bulk of buying these synthetic DNA strands happens online, there’s a chance that the bad actor behind the initial hijack could also hijack that gene-procuring software, swapping out particular chunks of that requested code.
Technically, synthetic DNA suppliers are required to check any sequence that’s requested against a massive federal database listing off particular “sequences of concern” that could be used to create, say, a deadly chemical agent or potential bioweapon. But these guidelines are both pretty poorly enforced, and pretty easy to bypass through the same sort of obfuscation beloved by bad actors in the tech sector. By muddying their request in this way, the Israeli team was able to put in an order for a particularly toxic peptide from a major synthetic bio company, and that company’s screening software completely skipped over the shady sequences. The team even had their order moved onto the production line before they contacted the company to cancel it.
Going back to our nameless bioengineer from earlier, it’s entirely possible that her hacked computer could put in a similarly faulty order, only to pass with similarly flying colours. If the resulting genetic sequence ends up in her hands — and she ends up injecting said sequence into a cell — she could end up producing something potentially harmful, rather than the chunk of the vaccine that she (supposedly) ordered.
The overall market for synthetic biology is expected to rocket past $US19 ($26) billion dollars over the next five years. Some of the companies in this space have earned massive valuations on their own.
Of course, the scenario described in the letter is less of an immediate threat, and more the kind of thing that should be a wake up call for the buyers and suppliers in the synthetic biology business. But frankly, it’s a wake up call that they could both use.
