As many incarcerated individuals are having their visiting privileges restricted due to the global pandemic, Telmate’s Getting Out app has become one of the only options that families separated by incarceration have to keep in touch. But according to research published today, hundreds of millions of intimate messages from many millions of inmates were sitting exposed on the web.
The Getting Out app alleges to provide “simple and reliable communication between inmates, friends and family” by charging up to $US0.50 (70c) per minute for families to communicate with their incarcerated loved ones — who are increasingly kept in dangerous and inhumane conditions. While its customers might reasonably expect that their communications could be monitored by prison officials, that their messages were available to anyone who found them on the internet is indicative of a type of negligence in line with previous reporting about the company.
In April Gizmodo reported that errors in Telmate’s Guardian app were likely landing parolee’s back in prison. Later in the month Gizmodo notified Guardian’s developers about a misconfigured Amazon S3 Bucket they had used for testing their Getting Out software.
“GTL ( Global Tel Link ) has a long history of overcharging loved ones of incarcerated people for phone services” James Kilgore, director of Media Justice’s Challenging E-Carceration project, said in an email. “Their ventures into GPS tracking both add illicit funds to their revenue stream and extend the boundaries of e-carceration, the use of technology to deprive people of their liberty. They are among the worst of the prison profiteers.”
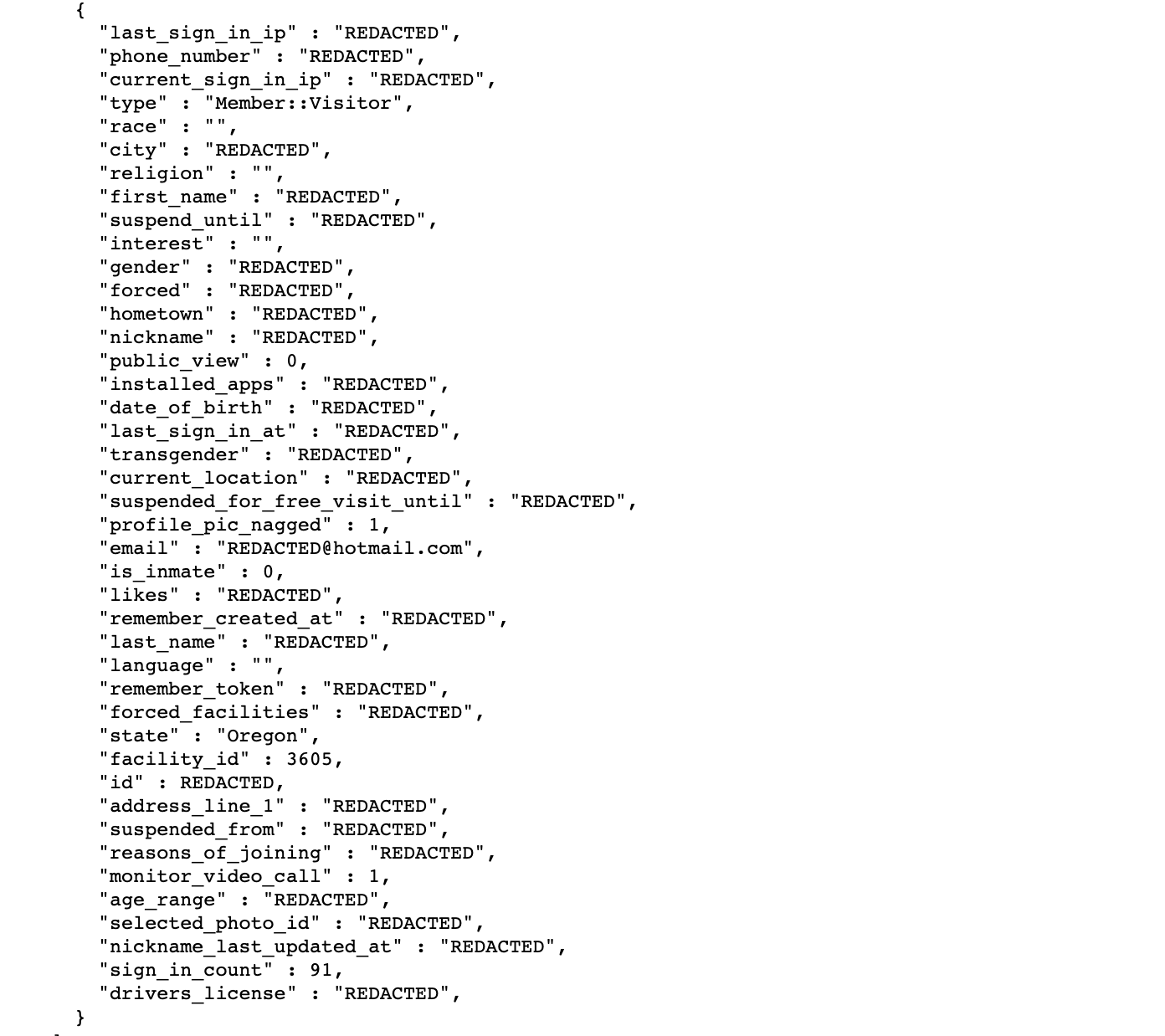
The leak was first discovered by a CompariTech security researcher named Bob Diachenko, who shared a redacted sample of the exposed data with Gizmodo. It appears that along with the contents of the inmate’s communications, the exposed data contains detailed information about each inmate and who they were communicating with.
Offering a striking view into the amount of data that is kept on the almost 2.3 million people incarcerated in the U.S., the data includes, among other things, whether an inmate identifies as transgender, their relationship status, prescription medication they take, and their religion. Global Tel Link did not respond to specific questions about the granularity of the data they retain.
In an email, Global Tel Link blamed “the actions of one of our vendors” for the exposed data. “This vulnerability was swiftly corrected, the data security system was immediately supplemented with the assistance of third-party consultants, and we continue to work closely with law enforcement authorities as we conduct further inquiry into this incident,” the company added. “Based on the current facts of the investigation, no medical data, passwords, or consumer payment information were affected.”
The company said it is contacting affected users and assured that “we are committed to doing everything we can” to secure its data.
Comparitech estimates the exposure impacts prisoners in facilities located everywhere that GTL operates and 90 per cent of the prison telecommunication market is split between Securus and GTL. In total, 11,210,948 inmate records and 227,770,157 messages were exposed, according to Diachenko’s findings.
While Global Tel Link isolated and secured the leak the day that Diachenko discovered the database, it is unknown how long the data had been sitting unsecured.
”At the core of all these exposures lies a human mistake,” Diachenko said in a video call interview. “Amazon, Microsoft, Elastic, Mongo, have all introduced pretty strict security policies that make customer data private by default. In order to make this public it had to be done manually. At the end of the day it’s often not a service that makes mistakes, but a person.”
