Among the blizzard of news bits from Apple’s WWDC, a much-anticipated feature has returned to the beta for iOS 12: A mode for keeping the FBI and other snoopers out of your phone. The feature has come and gone in the past, but it’s looking more real and better than ever this time around. Still, I’ll believe it when it’s actually live.
Photo: Getty
“USB Restricted Mode” has been spotted in previous iOS betas, but has never made it to a public release. It’s one of the most hotly anticipated features for security experts because it promises to be a major obstacle for iPhone hacking tools – such as GrayKey and Cellebrite – that law enforcement has been using to break into encrypted phones.
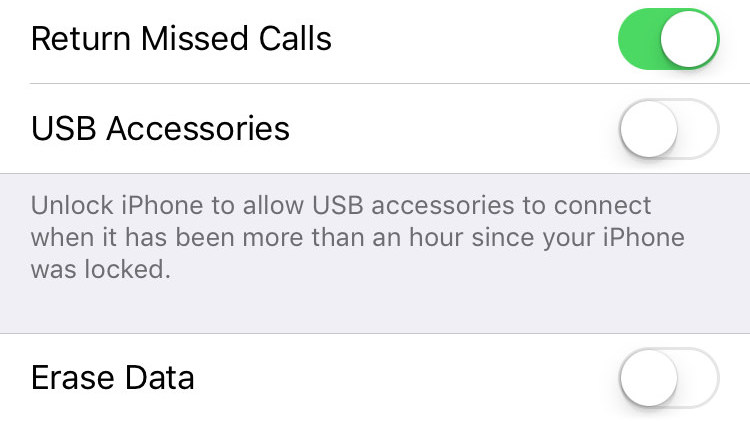
With the announcement of iOS 12, developers are getting their first look at the latest iteration of Apple’s mobile OS, and we now have a screenshot of the settings menu where you can turn USB Restricted Mode on or off.
Screenshot: Via Motherboard
The mode is designed to disable USB connectivity on the iPhone after it goes a certain amount of time without being unlocked. In previous iterations, the time limit was seven days, but it now appears that it will only be an hour. The security feature is also mentioned in the release notes for iOS 12 beta.
The public doesn’t know for certain how the iPhone cracking services that law enforcement uses actually work. But researchers at Elcomsoft explained the general theory last month:
Before iOS 11, one could use an existing lockdown record to access the iPhone or iPad device for the purpose of creating a new local backup (logical acquisition). Essentially, this is exactly how experts perform logical acquisition in the vast majority of cases of iPhone and iPad devices that are locked with an unknown passcode. The lockdown record (a small file extracted from the suspect’s computer) allows accessing essential information about the device and initiating the backup sequence without the passcode.
In addition to iTunes-style backups, the lockdown record could be used for pulling media files (pictures and videos), list installed apps, and access general information about the device.
Apple has already introduced a seven-day time limit on how long lockdown records last, but with USB Restricted Mode it will be all but impossible to access them after an hour without using the numerical passcode for the phone.
Yes, enabling this mode means you’ll probably have to punch in your passcode more often, and it will complicate that (really convenient) Face ID thing, but having bad actors break into your phone is no fun either. FBI or not, better-encrypted protection is just an all-around good thing.
We’ve asked Apple if it intends to include the feature in iOS 12’s public release this spring, but did not receive an immediate reply. Ryan Duff, Director of Cyber Solutions at Point3 Security, told Motherboard he believes Apple is just getting a feel for what the best execution of the tool will be.
“They definitely don’t want the scandal of removing a security feature because of something they didn’t anticipate,” he speculated.
Apple is also likely nervous about what the reaction from law enforcement will be. Despite the expert consensus that a built-in encryption backdoor for the government will make everyone less safe, the FBI continues to make its case that it urgently needs one. That case was severely weakened in March when the agency admitted it was using totally inaccurate statistics for the number of devices it had on hand that couldn’t be cracked. It attributed the miscount to “programming errors”.
All we can say is wait and see on this feature, but keep an eye out for it this spring. You’ll definitely want to turn it on as soon as it’s out.
