A new survey of IT professionals this week offers some deep insight into the premier challenges facing industries worldwide, from across the threat landscape.
A screenshot of the warning screen from a purported ransomware attack, as captured by a computer user in Taiwan. Photo: AP
More than 1000 security employees in as many as 17 countries participated in the survey. Most said the biggest hurdle to mounting an adequate defence against cyber threats today is the lack of skilled personnel. (Poor security awareness and an inability to sift through enormous piles of data tied for second place.)
The survey, which included 1200 respondents working in 19 industries, was compiled by CyberEdge Group, a research and marketing firm serving high-tech vendors and service providers.
More interesting is the feedback collected from respondents who said their organisations were infected with ransomware in the last year. (Ransomware tied with phishing attacks for the second most crucial security concern; the first, as per usual, is malware.)
Slightly more than half of the respondents’ organisations that actually paid a ransom to recover stolen or encrypted data – either in Bitcoin or some other anonymous currency – were unable to recover their data. In total, the report says, a little under 39 per cent of the organisations resolved to pay.
“Flip a coin once to determine whether your organisation will be affected by ransomware,” CyberEdge suggests. “If it will be, flip it again to determine whether paying the ransom will actually get your data back.”
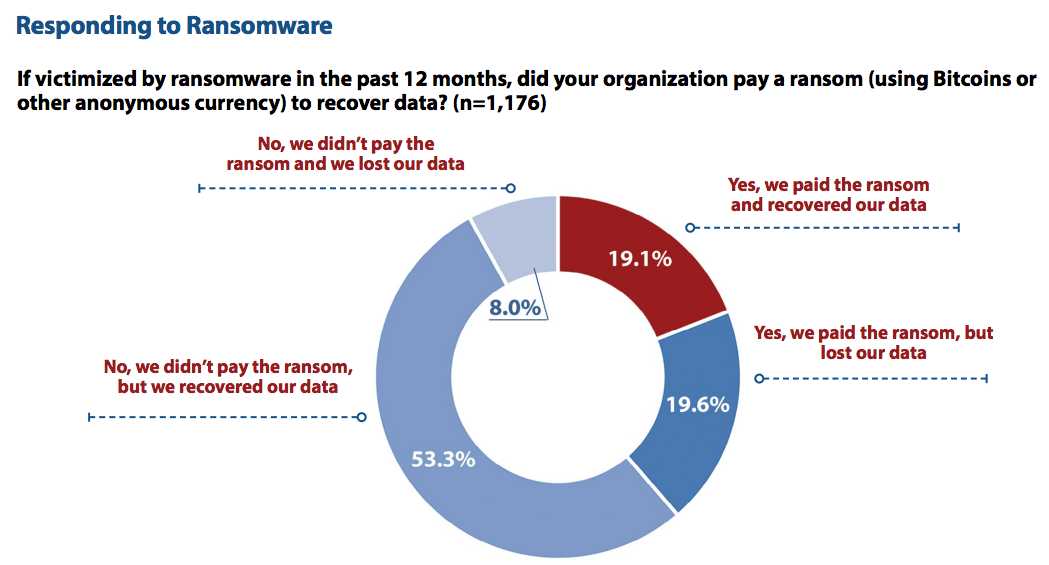
Graphic: CyberEdge Group
Notably, the respondents said that of organisations that opted not to pay the ransom, only 13 per cent were unable to recover their data. That 53 per cent of ransomware victims managed to recover their data without paying is likely attributable to the use of offline backups.
Spain tops the list of countries most affected by ransomware, followed closely by China and then Mexico. Only 46 per cent of Australia-based respondents said their organisations had been affected, which places Australia in the bottom three.
In decreasing order of frequency, the industries most affected by ransomware in 2017 were, according to the report: Education, telecom and technology, manufacturing, retail, finance, government, and healthcare. Mid-sized organisations (5000-9999 employees) were affected the most, while those with between 500 and 999 employees were affected the least.
Ninety-one per cent of the respondents aired one or more concerns about their companies’ data being migrated to the cloud. Maintaining regulatory compliance was last on their minds, while data privacy and confidentiality was of utmost concern. Controlling access to cloud data also ranked high on the list.
When it comes to vulnerability patching, roughly a third of the respondents said the biggest hindrance was finding time to take production systems offline. Nearly an equal number complained about a lack of qualified personnel. Remarkably, more than 20 per cent acknowledged that patching takes a backseat to other security initiatives.
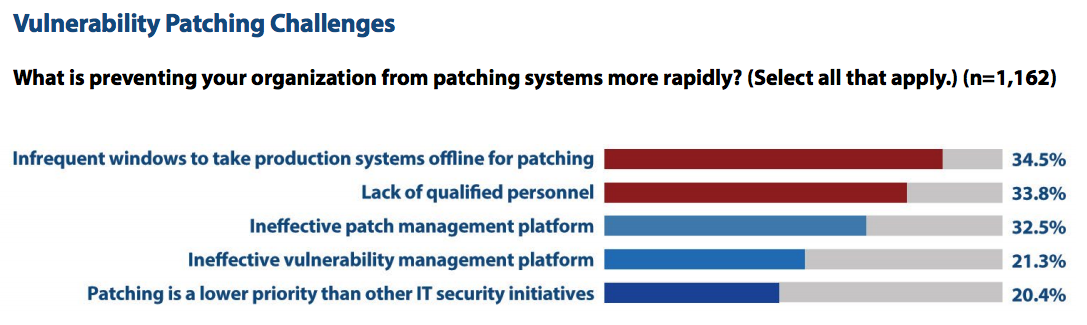
Graphic: CyberEdge Group
Respondents in the Australia said their organisations allocate 11.2 per cent of their overall IT budgets to security, meaning they spend the fourth least of the countries surveyed. Mexico allocates the most at 15.6 per cent, and organisations in Germany, Singapore and Japan apparently designate the smallest percentage. (The global mean is 12.1 per cent)
Generally speaking, the more employees, the greater the percentage of the budget earmarked for security. In no country did more than 5.6 per cent of IT employees expect to see an increase in the security budget.
Only 68.3 per cent of respondents said their organisations had network-based antivirus software deployed – and of those who don’t, nine per cent said there was no plans to deploy it in the future. More than 33 per cent of the organisations apparently aren’t using a web application firewall and nearly 40 per cent aren’t running any kind of intrusion detection system.
When it comes to endpoint security guarding desktops, laptops and servers against threats, around 32 per cent of respondents said their organisations aren’t running basic anti-malware software, and nearly 43 per cent said they have no data loss or leak prevention protocols in place.
Deception technology (“honeypots”), which is one of the most useful tools for detecting hackers post-breach, is only used by roughly 47 per cent of the respondents’ companies – more than 20 per cent said they have no plans to use it.
“Mitigating today’s cyber threat risks takes more than investing in the right technologies,” CyberEdge notes. “You must ensure those technologies are both deployed optimally, configured correctly, and monitored adequately to give your organisation a fighting chance of not making tomorrow’s front page news.”
Good luck!