Ashley Madison is perhaps most famous for two things – infidelity and godawful security. In 2015, the website for cheaters was hacked, leaking almost 10 gigabytes of data on the dark web, which included account details, email addresses and payment information for about 32 million users. And now security researchers have found that the dating site is still exposing user data, only now it isn’t because of hackers. The site just has crap security settings.
Photo: Getty
Users on Ashley Madison can include both public and private photos on their profile – public photos are available to any user, whereas private photos are only available to users who have been sent a “key”. The Kromtech Security team worked with independent security researcher Matt Svensson to investigate security flaws on the Ashley Madison site, and found that the default setting automatically shares your key with another user if they share it with you. What’s more, these private photos can be accessed through a URL, which the security researchers point out is too long to brute force.
While users can opt out of automatically sending their key, most likely don’t. That’s because of what the security researchers point out as the “tyranny of the default”, or the idea that people tend to maintain the recommended default settings. The researchers tested out this theory, giving a key to “a random sample of users that had private pictures”, and found that 64 per cent of these accounts had private photos that would automatically return a key.
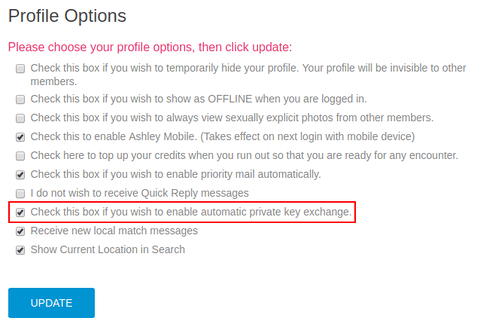
Photo: MacKeeper
The researchers noted that they disclosed the security issues to Ashley Madison. In response, the company has limited the amount of daily key exchanges. But automatic picture sharing remains because Ashley Madison’s parent company, Avid Life Media, “does not agree and sees the automatic key exchange as an intended feature”. When I asked Kromtech Security Team what reason Ashley Madison had for not revoking the automatic key exchange feature, head of communications Bob Diachenko said that it was a low-to-medium threat for the average user, “but could be high for those with explicit photos, those that were involved in the prior leak, or those that can be de-anonymized via pictures or username. A ‘The Fappening’ type dump is the worst case scenario, side by side with blackmail after tying nude photos to the prior leak.”
It’s important to note that Ashley Madison is willingly going against the recommendations of security experts. Recommendations that would benefit its most vulnerable users – women.
