In the latest leak of sensitive medical records in the United States, lab test results and other patient files belonging to an estimated 150,000 Americans were unearthed online by security researchers late last month.
Photo: Getty
The records, discovered by researchers at the Kromtech Security Center, had been stored on an unsecured Amazon S3 bucket. According to Kromtech, the files were publicly accessible and were not protected by a password. A cursory examination of the contents revealed a wide range of sensitive details about patients whose names, addresses, phone numbers, diagnoses, and test results were exposed.
The files have been linked to a healthcare services company, Patient Home Monitoring Corporation (PHM), a division of which provides US patients with in-home monitoring and disease management services. The data breach contained about 47.5 GB-worth of data composed of roughly 316,000 PDF files.
The breach was first discovered on September 29th, Kromtech security researcher Bob Diachenko told Gizmodo. On October 5th, PHM was alerted that sensitive medical records belonging to the company had been exposed. Following notification, the bucket was secured on the same day. PHM did not, however, respond to Kromtech’s inquiries.
“This Amazon repository was misconfigured to be publicly available and anyone with an internet connection could access these confidential medical records,” said Alex Kernishniuk, Kromtech’s vice president of strategic alliances. “Even the most basic security measures would have prevented this data breach.”
As with most data breaches involving Amazon servers, it’s not immediately clear for how long the files had been exposed — or whether the records were downloaded by anyone else before the company was notified. According to Kromtech, the records appear mostly related to tests conducted over the course of this summer.
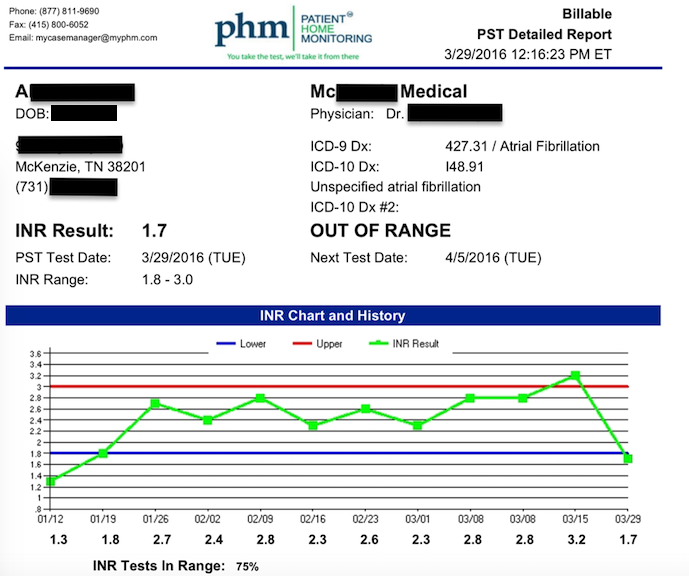
One of the leaked records reviewed by Gizmodo revealed a patient living in Tennessee who had been diagnosed with atrial fibrillation, a serious condition characterised by irregular heartbeat (arrhythmia) known to cause heart failure, stroke, among a host of other serious health risks. The record showed that the patient had been conducting a series of at-home blood tests designed to warn physicians of health complications, such as blood clots and uncontrolled bleeding typically associated with blood thinning medications. (The patient’s identity was redacted by Kromtech prior to review.)
In addition to names, addresses, and other contact information, many of the records contained dates of birth, diagnoses, as well as the names of physicians overseeing the patients’ care — information subject to strict safeguards under the Health Insurance Portability and Accountability Act (HIPAA). Covered entities, such as PHM, are required under the law to develop and implement policies and procedures to protect electronic protected health information (ePHI) which the entities “create, receive, maintain, or transmit.”
Under HIPAA’s Breach Notification Rule, healthcare providers are required to notify patients affected by a data breach “without unreasonable delay” and “no later than 60 days following the discovery of the breach.” Additionally, if the provider has “insufficient” or out-of-date contact information for 10 or more patients, they are required to post notification of the breach on their website for at least 90 days or circulate information about the breach to major print and broadcast media outlets in areas where the affected patients reside.
What’s more, the provider is required under HIPAA to notify major media outlets in any jurisdiction or state where more than 500 affected patients reside.
HIPAA violations also carry financial penalties. In cases where the provider couldn’t reasonably be expected to know about the breach, the fines can be as low as $US100 ($129) per incident; but in extreme circumstances, where the provider is found to have acted with “willful neglect,” fines can reach up to $US1.5 ($2) million per year for each violation.
Gizmodo reached out to a PHM employee on Tuesday but did not immediately receive a response.
Kromtech has previously disclosed and helped to secure several data breaches involving protected health information. Earlier this year, the company discovered tens of thousands (if not millions) of medical records online that originated from the Bronx-Lebanon Hospital Center in New York. Those records included a wide range of highly sensitive patient files, including addiction in-take forms for patients enrolled in the hospital’s chemical dependency program.
Kromtech’s Diachenko told Gizmodo that the company offers free software designed to let companies know whether their Amazon buckets are secure or not.
“Sadly the US has the most expensive, least effective health care system by nearly every measurement,” Kromtech said in a statement Tuesday. “Complex insurance rules and distorted market signals create massive inefficiencies, frustrated patients, and providers burdened by excessive paperwork. No one will deny that digital records and patient home monitoring could bring some much needed efficiency, however protecting that valuable medical data is a priority that must be taken seriously.”
