Security researchers last month discovered a trove of scanned images depicting the credit cards and passports of more than 88,600 international travellers. It’s unknown for how long the documents, which were secured on Thursday, had been sitting online, just waiting to be stolen.
Photo: Getty
Researchers at the Kromtech Security Center say a cache of more than 300GB worth of sensitive records discovered in mid-August is linked to MoneyBack, a company that offers refunds on sales and other value-added taxes on goods purchased by travellers to Mexico.
On a server located in the United States, the company had stored more than 455,000 documents, including scanned images of credit cards, travel receipts, airline tickets, passports and other government-issued ID cards.
Passports identified by Kromtech belong to citizens of the US, Canada, Argentina, Colombia and Italy, among many other countries.
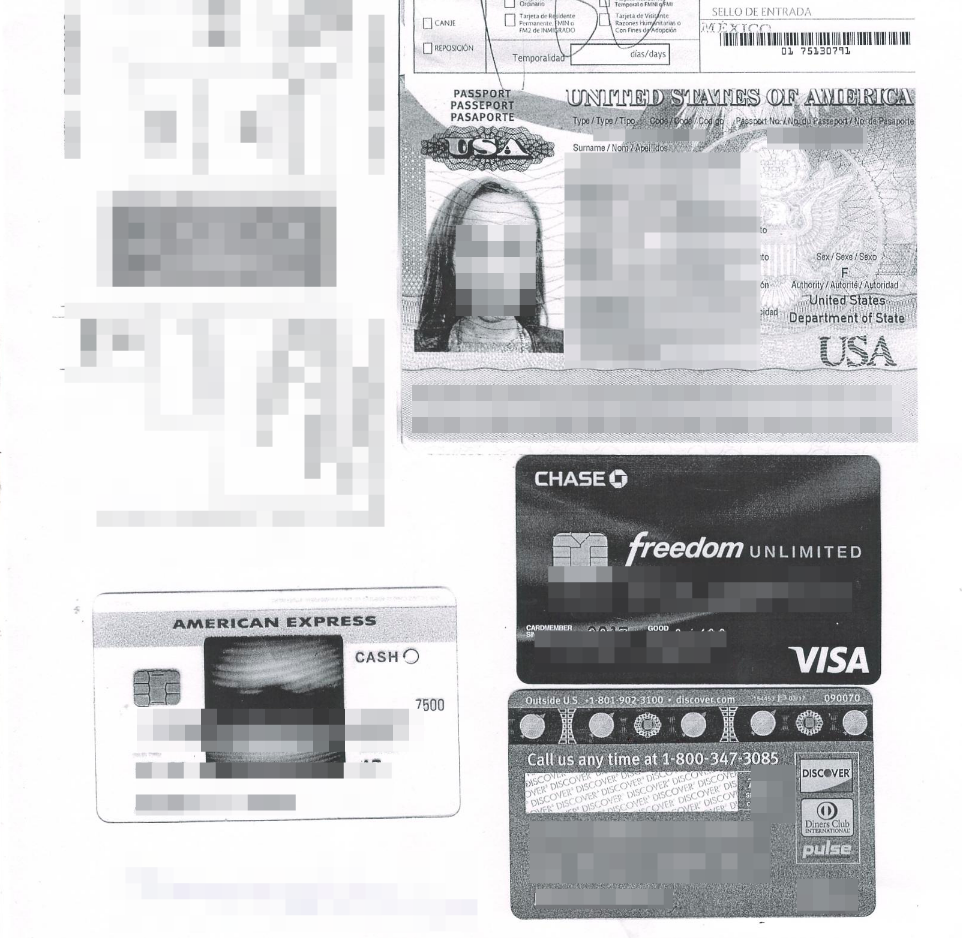
A credit card and passport scan exposed by the MoneyBack data breach (Kromtech)
To encourage tourism, Mexico is one of several countries offering tax refunds to travellers who spend a minimum amount on goods in the country from participating stores. To qualify, tourists in Mexico must spend at least 1200 pesos ($84), enter the country by sea or by air from certain airports, and register with MoneyBack at an airport or cruise ship terminal.
To receive a refund on the qualifying taxed goods, MoneyBack requires travellers to cough up a slew of documents containing sensitive information, including boarding passes or cruise IDs for departure, receipts for their purchases along with credit card vouchers, and passports and other immigration forms.
According to Kromtech, MoneyBack stored these records in a database (CouchDB) that was misconfigured, which allowed essentially anyone to access them, even through a web browser. It’s unknown how long the documents were exposed, but Kromtech says metadata on some of the files dates back to late 2015. The most recent records are dated May 2017.
After being alerted to issue, MoneyBack quickly secured the database, closing off a port (5984) that enabled public access. The company did not reply to Kromtech’s emails, however, nor has it responded to a request for comment from Gizmodo.
“Cyber criminals could have all of the information they would need to commit identity fraud or use the hundreds of thousands of credit card numbers that were in the database,” said Alex Kernishniuk, Kromtech’s VP of strategic alliances. “This is once again a warning to companies or organisations who collect sensitive data to take every possible step to ensure that proper data security measures are used.”
Added Kernishniuk: “Time and time again simple human errors that could be easily avoided expose sensitive data on the internet. It is unclear if anyone other than security researchers accessed the data or how MoneyBack will notify their customers around the globe that their data has been exposed.”
Late last week, Kromtech’s researchers discovered and helped secure more than four million records containing the personal details of Time Warner Cable (TWC) customers, which had been improperly stored on an Amazon S3 bucket without the protection of a password.
[Kromtech]
