Earlier this week, reports emerged that the head of the Ukrainian Cyber Police is seeking criminal charges against the Ukrainian tax software company that was the first victim of the crippling NotPetya malware attack. Now, it has come to light that the firm’s servers have been seized by authorities.
Photo: Getty
[referenced url=”https://gizmodo.com.au/2017/07/nato-considering-petya-malware-a-potential-act-of-war/” thumb=”https://i.kinja-img.com/gawker-media/image/upload/t_ku-large/wj6j5ne9vdwnzlam2wzm.jpg” title=”NATO Considering ‘Petya’ Malware A Potential Act Of War” excerpt=”On Saturday, Kevin Scheid, a Department of Defence veteran, was placed in charge of NATO’s cyber operations. The appointment wouldn’t be big news if it weren’t for the fact that he’s joining the organisation at a hair-raising point in history. The vicious malware triggered NATO to announce on Friday that the attack is believed to be the work of a state actor and is a potential act of war.”]
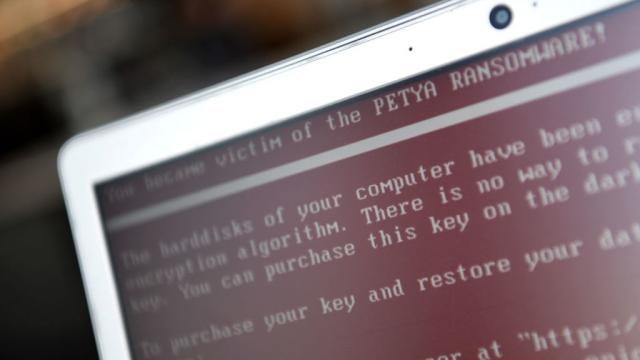
Last week, a vicious piece of malware began spreading around the globe that was initially believed to be ransomware but is now understood to be a wiper. Researchers traced the origin of what’s come to be known as NotPetya back to a software firm called MeDoc. Ukraine’s most popular tax preparation software, MeDoc is one of only two programs that are officially authorised by the Ukraine government. While no one has accused the firm of intentionally spreading the worm, it’s believed that it was first pushed out through a software update to the tax software. Because it’s tax season in Ukraine, this was a very effective strategy for the hackers who are responsible.
Yesterday, authorities raided MeDoc and seized its servers as part of an ongoing investigation into the attack. Police believe that the operation was planned months in advance, and security firm ESET has determined that a backdoor was written into WeDoc’s updates. ESET researcher Anton Cherepanov says it’s likely that the hackers who are responsible had access to WeDoc’s source code. That report traces the first injection of a backdoor vulnerability to April 14.
Col. Serhiy Demydiuk, the head of Ukraine’s national Cyberpolice unit, has not accused anyone at MeDoc of being involved with the attack. He has said that the company was warned multiple times about potential security vulnerabilities in its systems. “They knew about it,” Demydiuk told the Associated Press. “They were told many times by various anti-virus firms… For this neglect, the people in this case will face criminal responsibility.”
The family that founded MeDoc has denied any wrongdoing. “We studied and analysed our product for signs of hacking — it is not infected with a virus and everything is fine, it is safe,” Olesya Linnik, one of the developers of the software tells the Associated Press. “The update package, which was sent out long before the virus was spread, we checked it 100 times and everything is fine.”
Independent security analyst Jonathan Nichols confirmed on Monday that he’d found several publicly known vulnerabilities in MeDoc’s update servers. He did not test the vulnerabilities out of fear of committing a crime. He does conclude that the attack could have potentially been executed by an individual or a group that isn’t particularly skilled. That’s an important point because NATO has gone on record saying that its research points toward a state actor being responsible. And Ukrainian intelligence has accused Russian security services of masterminding the operation. The Kremlin has denied the charges.
Meanwhile, corporate victims have begun to recover from the attack and NATO has brought in new equipment to help Ukraine defend against future cyber attacks. Eighty per cent of companies in Ukraine use the MeDoc software and the country’s parliament is working to extend tax deadlines in order to account for the messy disruption.