Photo: Getty
On Wednesday, WikiLeaks released the latest issue in its ongoing Vault 7 series — a trove of secret or otherwise classified US Central Intelligence Agency files from 2013 to 2016 describing previously undisclosed malware and viruses.
Today’s release includes documentation on “ELSA,” a purported CIA project for tracking human targets carrying wi-fi-enabled devices. The malware involved in this project is specifically for devices running Microsoft Windows.
As with the rest of the Vault 7 material, the 42-page “ELSA” manual
was allegedly stolen from the agency’s Center for Cyber Intelligence in Langley, Virginia. The method “ELSA” supposedly employs to determine a Windows user’s location is pretty ingenious, though not an entirely new idea.
The first step involves injecting the target’s laptop with geo-location malware. Once installed, the malware begins scanning for and collecting metadata from nearby wi-fi networks. This information can be collected from the surrounding networks as long as wi-fi is enabled on the device — a connection is not required.
Using this data, it is possible — with varying degrees of success, no doubt — to locate a target using what’s called trilateration. Basically, the signal strength of the wi-fi network is used to approximate the distance of the target from the network device’s wi-fi transmitter. This is very similar to how law enforcement locates a suspect via his or her mobile phone by measuring the signal strength of multiple nearby cell towers.
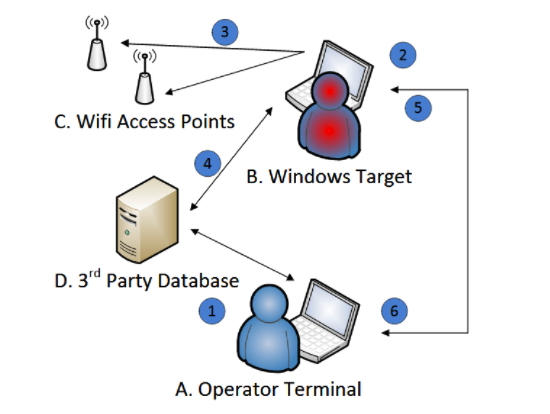
A standard wi-fi transmitter has a range of about 32.00m. Measured by the target’s device, the signal strength will, therefore, tell the “ELSA” operator (CIA) approximately where the target is. If the signal is very strong, then the target is probably within 10 to 15 yards of the transmitter; as the signal begins to fade, the operator can conclude that the target is moving away from the transmitter. If the person is within the range of multiple wi-fi networks, you can combine the data collected from various networks to generate a more accurate picture of the target’s relative location.
There’s no indication as to how often the “ELSA” program was or is used, but it’s easy to see how this would be a useful tool for the nation’s clandestine agency. For instance, it seems like a fairly effective way to identify a person’s relative location — say, if you were planning a drone strike.
As part of its Vault 7 series, WikiLeaks has previously revealed similar documents showing how CIA performs various man-in-the-middle (MitM) attacks and hacks mobile phones and Samsung smart TVs. According to WikiLeaks, the quantity of the Vault 7 leak, which the publisher is doling out month by month, “already eclipses the total number of pages published over the first three years of the Edward Snowden NSA leaks.”