Most people know the “I’m not a robot” single-click version of CAPTCHA which is able to identify that a user is human by the way that they move their mouse. Researchers have now found a way to apply that principle to catching identity thieves in the act.
Image Source: Monopoly
[referenced url=”https://gizmodo.com.au/2017/03/google-has-finally-killed-the-captcha/” thumb=”https://i.kinja-img.com/gawker-media/image/upload/t_ku-large/ilvnurvjf866y48z6acw.jpg” title=”Google Has Finally Killed The CAPTCHA” excerpt=”CAPTCHA’s are an irritating but necessary evil. The system that is used to verify whether or not a user is human has been around a while and it had to evolve because machines were getting better at reading the text than humans. With its latest iteration, Google says you’ll no longer have to input anything at all.”]
One of the biggest issues with identity theft is that if a person has successfully gotten ahold of your personal details, they could use them over and over again. Questions like “what’s your mother’s maiden name?” have evolved into more elaborate queries like “On which of the following streets have you lived?” But even the second question is easily referencable by a motivated identity thief.
That problem is being addressed by a team that recently published the findings of their new study in PLoS One. The mechanism for preventing identity theft is fairly simple but it represents some progress in a field with a lot of potential.
The researchers asked a group of 40 people from Italy (yes, it’s a small sample size) to answer 6 expected questions, 6 unexpected questions, and 4 control questions that required a yes answer. They were given the same amounts of questions that required a no answer. Half of the group was asked to respond truthfully, while the other half was given a fake profile to memorise. The group that had to fake it was quizzed twice before the test began and they proved that they knew all of the information necessary to answer the questions accurately.
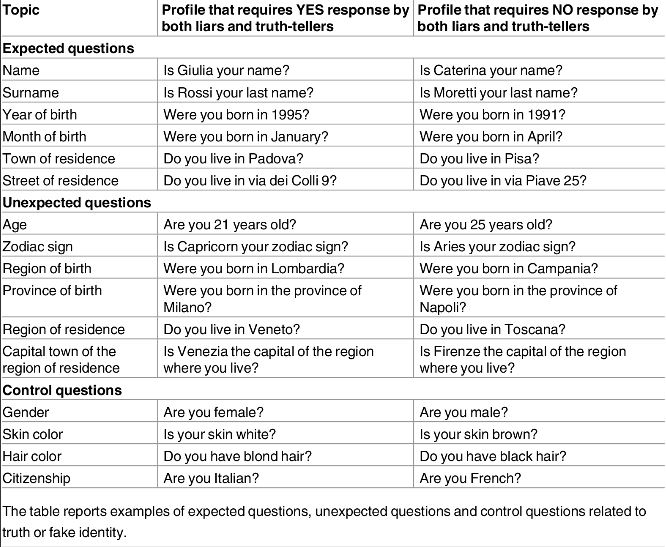
The list of yes/no questions. Image: PLoS One
By design, the liars would only have to lie on the non-control questions with a yes answer. Everyone did really well with the expected questions and only 2/240 were answered incorrectly. The unexpected questions were unsurprisingly more difficult with the people telling the truth getting 5/240 wrong and the liars getting 82/240 wrong.
While the participants were taking the quiz, mouse tracking software was following their movements and a machine learning algorithm (explanation) was later used for analysis. The participants weren’t being tested on their response times, though that could also be theoretically factored into this type of system. Obviously, if you know a fake birth date but not the corresponding zodiac sign you’d have to think about it or look it up.
What the researchers found was that the liars had a distinctive average mouse movement that was more circuitous than the truth tellers. Even when the liars were telling the truth, it seems that their overall dishonesty was infecting their movements and they could accurately be identified as lying. The researchers then repeated their full experiment with 20 German-speaking subjects to test for cultural differences and they arrived at the same conclusions. They write:
From a cognitive point of view, what is interesting here is that, in the experimental design, the mind-set of the liars also extended its effects to questions when they were responding truthfully. To our knowledge, this pattern of results has never been reported before and could be an indication of the level of sensitivity of the technique of mouse-movement analysis.
The sample here is too small and the testing procedures are too limited to indicate that this is a viable technique for detecting identity fraud. Plenty more research will have to be done and lots of algorithmic refinement will be necessary to make this in any way trustworthy. But it’s an interesting result for a new method and imagine what companies that have access to huge amounts of data could do. How distinct is a users mouse movement?
How distinct is it when you know how they respond to various stimulation for hours at a time over the course of years? It seems possible that with machine learning we could one day be analysing mouse movements as a virtual fingerprint across the web.