Adam Johnston and Scott Spriggs may well go down as Ohio’s cleverest inmates.
The ceiling area once housing the computers. Image: Ohio Inspector General
The pair were incarcerated at Marion Correctional Institution, a low-security, 2500-capacity facility which used inmate labour to recycle old computers as part of the non-profit RET3 program. Spriggs and Johnson managed to squirrel away dozens of RET3 parts and construct two new machines inside MCI.
According to the 50-page Ohio Inspector General report, the fully functional computers were “hidden on a plywood board in the ceiling above a closet” and subsequently “connected to [Ohio Department of Rehabilitation and Correction’s] computer network”. But wait — there’s more.
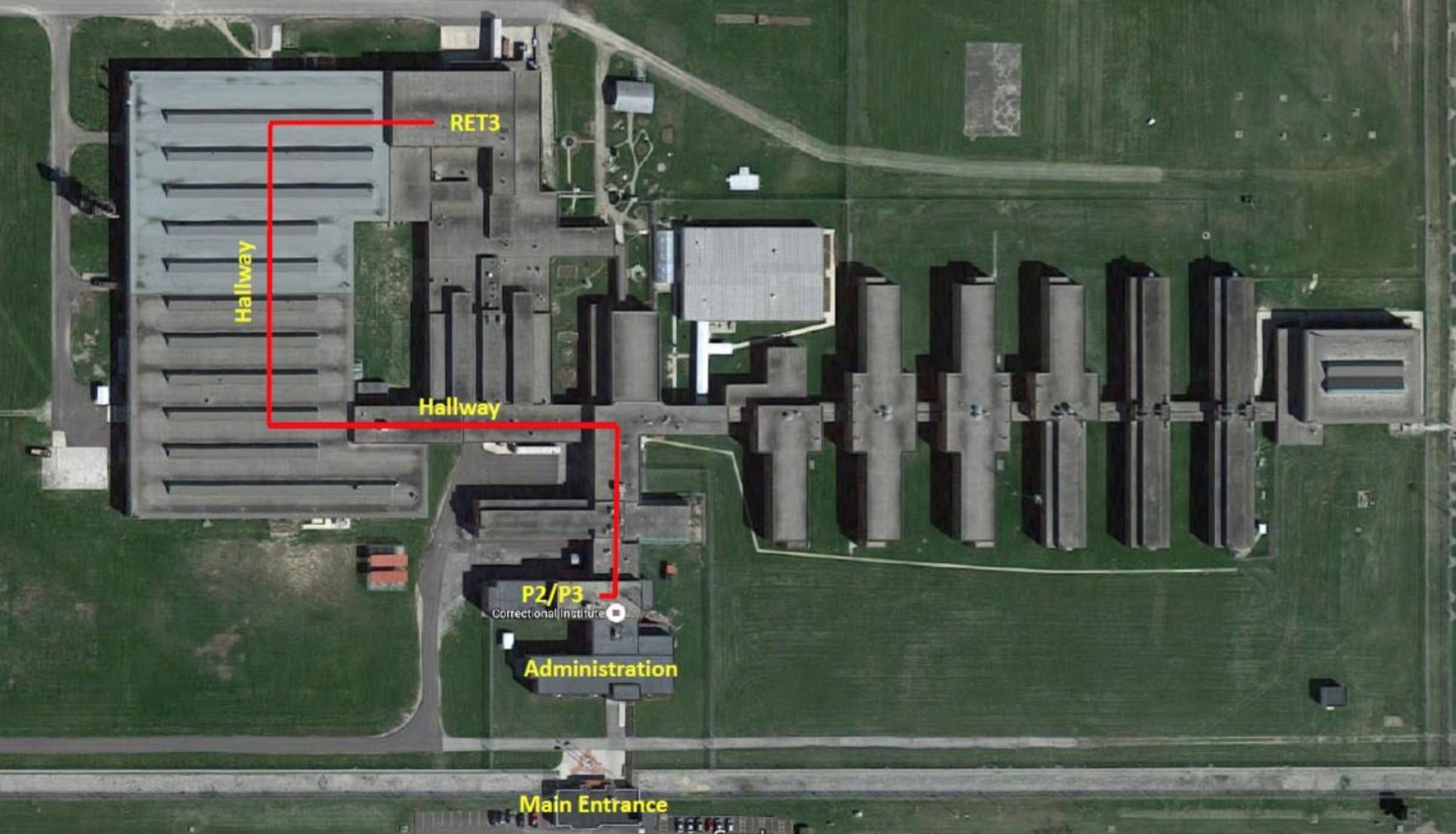
Here’s how far they had to carry the stolen parts. Image: Ohio Inspector General
Somehow Spriggs and Johnson were able to run ethernet cables through the ceiling and down to the network switch, where it was connected to port 16, and the inmates were able to obtain internet access via credentials belonging to Ray Canterbury, a retired prison employee who now works for ODRC as a contractor. Once connected, they were able to download articles on “home-made drugs, plastics, explosives, and credit cards”. Johnson, according to the report, also “accessed an article online from the Bloomberg.com site detailing how to submit fraudulent tax returns and have the refunds wired to debit cards”, and stole the identity of another inmate and used his name and social security number to apply for five credit cards.
But wait, there’s more.
As one does with an internet connection, the inmates used their unfettered access to download a buttload of porn, ferrying it to inmates via a thumb drive. But the inmate caught with said thumb drive told investigators that “it was not just pornographic movies. It was like the new releases, TV series” as well as music.
Oh yes, there’s still more.
On these two homebrew machines investigators found a litany of software useful for hacking and encryption, as well as brute force password crackers, an email spamming program, and a Java-based tool used to commit man-in-the-middle attacks. Likely this cornucopia of illicit programs was how the pair were able to issue “passes for inmates to gain access to multiple areas within MCI” and gain access to “unauthorised inmate records including disciplinary records, sentencing data, and inmate locations”. Ho-lee crap.
Given that oversight at MCI is clearly lacking, the only way these two masterminds were caught at all was due to employee bandwidth throttling. Remember Ray Canterbury? An automated message informed MCI staff that on Friday 3 July 2015 “a computer operating through the ODRC computer network had exceeded a daily internet usage threshold”. The credentials were tied to Canterbury, who only worked Monday through Thursday. Considering the level of sneakiness required to build computers from scratch, run network cables, and steal someone’s identity, not looking up employee schedules is a spectacular own-goal.
The ring of prisoners involved with this data heist have been shipped off to other facilities, and MCI are shouldering the blame for not only allowing it to happen, but failing to notify Ohio State Highway Patrol as regulations apparently dictate.
You can read the full report below:
