This weekend, San Francisco’s Municipal Railway was savaged by hackers demanding over $US70,000 ($93,679) in bitcoins, leaving the metro system unable to collect fares. But the hack may be much more devastating for the transit agency, according to a list of servers allegedly compromised by the hackers and obtained by Gizmodo.
Getty
The list contains the names of 2212 servers supposedly compromised by the hackers. If true, it could add more validity to the hackers’ demands for money so that they won’t dump 30 gigabytes of Muni’s internal data. The list contains servers with cryptic names like “BBYH382” but also includes servers like “PAYROLLHPDC7600”, “MUNIMAIL1”, “MUNIMAIL2” and “QUICKBOOKS”, which likely refers to the popular accounting software. It’s unclear which — if any — of these servers have been accessed by the hackers. However, breaking into payroll, email and accounting servers could mean that these hackers gained access to a massive amount of personal information.
Reddit/Blorq
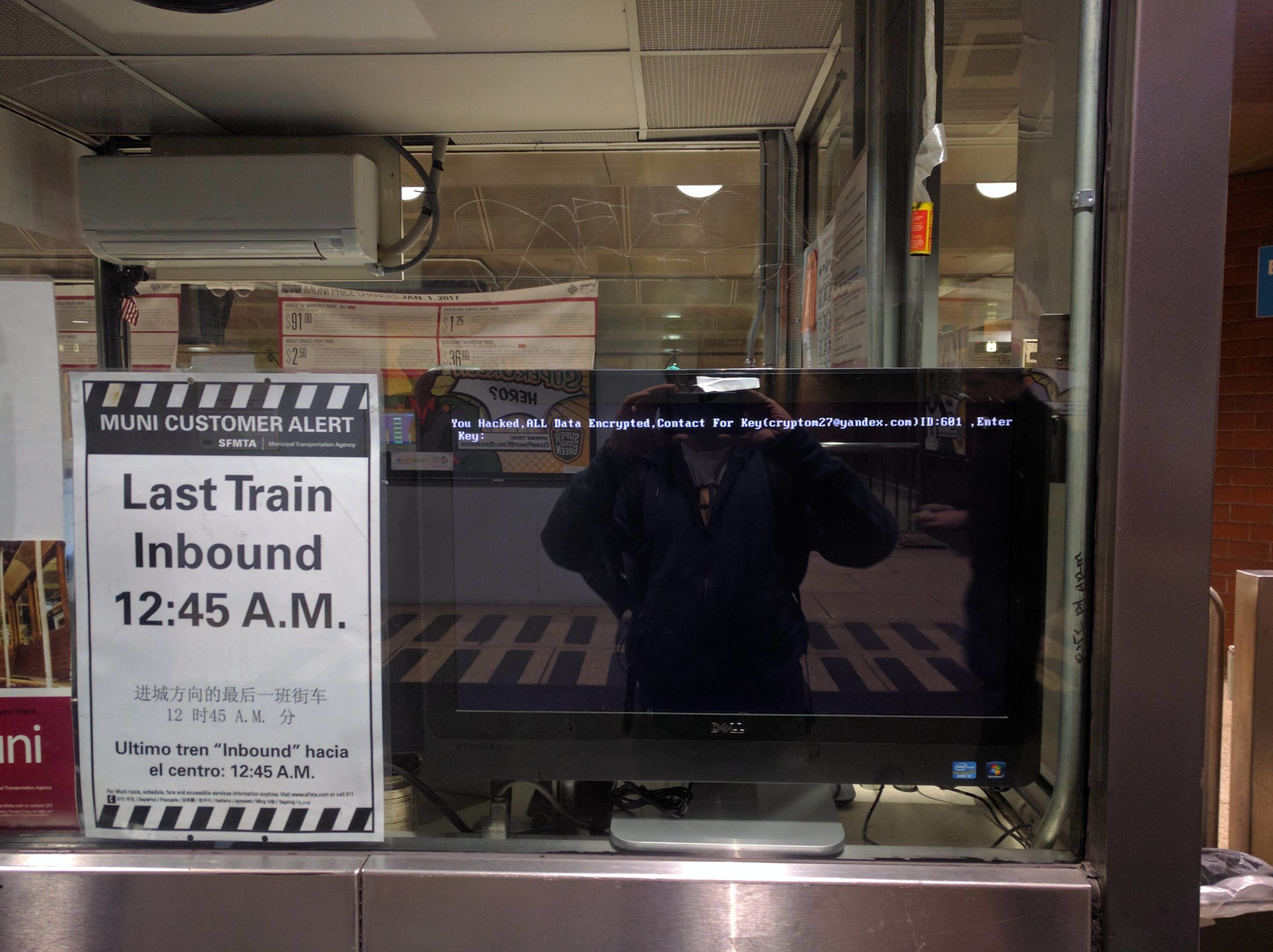
On Saturday, compromised machines within San Fransisco’s Muni stations displayed this message “You Hacked. ALL Data Encrypted. Contact For Key(crypton27@yandex.com) ,Enter Key:”. Bay Area-based IT manager and hobbyist security researcher Mike Grover reached out to the hackers, who assumed he was a Muni employee looking to negotiate a deal.
Grover provided this message he received from the hackers to Hoodline:
if You are Responsible in MUNI-RAILWAY !
All Your Computer’s/Server’s in MUNI-RAILWAY Domain Encrypted By AES 2048Bit!
We have 2000 Decryption Key !
Send 100BTC to My Bitcoin Wallet , then We Send you Decryption key For Your All Server’s HDD!!
We Only Accept Bitcoin , it’s So easy!
you can use Brokers to exchange your money to BTC ASAP
it’s Fast way!
The list of supposedly compromised servers also includes “GPOADMIN” and “gpoadmin2”. GPO stands for “Group Policy Object”, which is essentially a collection of settings and policies that are created and administered by server admins for machines on a network. Group Policy is also, funnily enough, a common way for hackers to distribute ransomware. If the hackers had access to these servers, it’s very possible that this is how they spread the virus.
Muni was able to un-hack their some of its systems by Sunday morning and was able to accept fares again. This only angered the hackers, who threatened to post 30 gigabytes of employee data in a message sent to journalists:
San Francisco People ride for free two days ! welcome !
But if ugly hacker’s attack to Operational Railways System’s , whats’ happen to You?
Anyone See Something like that in Hollywood Movies But it’s Completely Possible in Real World!
It’s Show to You and Proof of Concept , Company don’t pay Attention to Your Safety !
They give Your Money and everyday Rich more! But they don’t Pay for IT Security and using very old system’s !
We Hacked 2000 server/pc in SFMTA including all payment kiosk and internal Automation and Email and …!
We Gain Access Completely Random and Our Virus Working Automatically ! We Don’t Have Targeted Attack to them ! It’s wonderful !
If some Hacker Try to Hack Your Transportation Infrastructure Target-Based , it’s Have More Impact!
We Don’t live in USA but I hope Company Try to Fix it Correctly and We Can Advise Them But if they Don’t , We Will Publish 30G Databases and Documents include contracts , employees data , LLD Plans , customers and … to Have More Impact to Company To Force Them to do Right Job!
Hackers have a tendency to lie, and this statement seems like a last ditch effort to extort some bitcoin from Muni now that its systems are operating again. But if hackers actually have access to the servers included in this list, their ransom demands seem a little bit more serious.
The extent to which hackers compromised Muni systems remains unclear, but the idea of paying off hackers demanding bitcoins isn’t unprecedented. The Hollywood Presbyterian Medical Center did just that earlier this year, paying $US17,000 ($22,751) to regain access to its files. An FBI agent has even admitted that the agency “often [advises] people just to pay the ransom”.
Regardless of the details, this hack is particularly terrifying in that it targeted a transit system. If hackers can gain access to all of this data, including ticketing machines, how far away are they from being able to control or disrupt trains? Even if a hacker couldn’t go that far, the power to disrupt a major transit system could have catastrophic ramifications on a major metropolitan area. Let’s just hope other systems heed will heed last weekend’s warning.
