All electronic devices emit radio waves when they’re powered on, even if they don’t connect to the internet or Bluetooth. Governments have been using these accidental waves to spy on each other since the 1960s — but this week, a computer scientist at the Black Hat hacker conference took the idea way further than we’d thought possible.
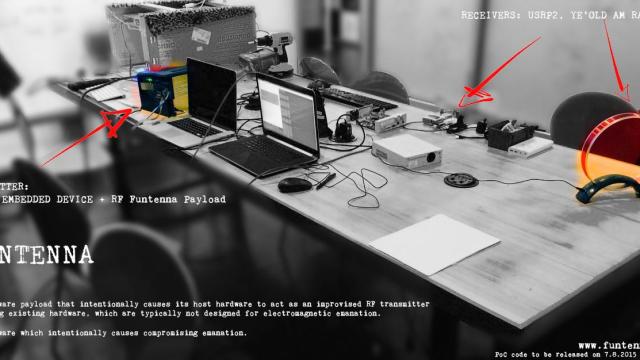
If you wanted to try to spy on someone using these emanations, you would pick them up and reconstruct them using specialised monitoring equipment. But what if you wanted to actually broadcast data from a device, even if that device isn’t even designed to communicate? That’s exactly what a scientist named Ang Cui has done with a project called Funtenna, which Cui presented this week at Black Hat in Las Vegas. Even crazier? He demo’d the idea using a regular old laser printer.
Using the old printer, Cui used a short bit of code to manipulate the power profile of the printer. Ars Technica’s Sean Gallagher, who was at the demonstration in Vegas, explains:
By rapidly flipping the power state of general purpose input/output (GPIO) pins, Pulse Width Modulation (PWM) outputs, and UART (serial) outputs on a Pantum P2502W laser printer — “the cheapest laser printer we could find,” Cui said — the Funtenna hack was able to create a modulated radio signal as a result of the magnetic fields created by the voltage and resulting electromagnetic waves.
Those signals could be picked up on a nearby AM radio. What did he transmit during the demo using this jerry-rigged printer-turned-radio-transmitter? Why, the first line of William Gibson’s Neuromancer, of course:
One of the most unsettling things about the project is that it could, in theory, be done with any electronic device — even those, as Cui apparently noted, that are air-gapped or not intended to be networked. We tend to think of devices that don’t connect to the internet as safe from attack — as it turns out, just being on is its own security issue.
[Funtenna; h/t Ars Technica]