The licence plate reader (LPR) cameras installed in most US cities allow police to track cars and their drivers who are potentially engaged in criminal activities. But depending on the way police store the data, it Ars Technica found out, anyone might be able to access this information.
We’ve been following this story closely, from the ACLU’s report on how police departments collect data to a federal DEA-sponsored program that likely has millions of plates (probably yours!) in its database. Over at Ars Technica, Cyrus Farivar managed to use California’s Public Records Act to obtain 4.6 million scans of 1.1 unique plates from the Oakland Police Department after attempting to find out how his own car had been tracked by several police departments.
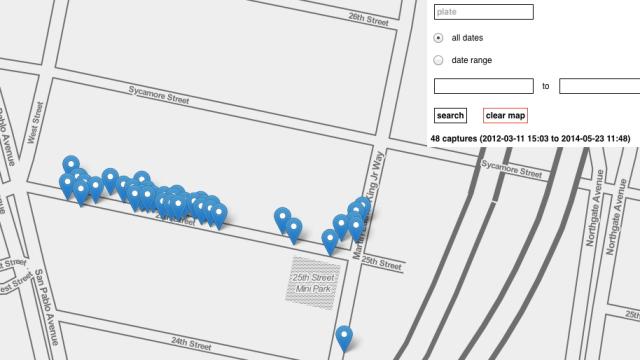
To illustrate just how much information police are gathering on the cars in their city, Farivar enlisted data visualisation designer Mike Tahani to take the 18 Excel documents from OPD and build a tool which plotted all the geotagged scans on a map, allowing him to search the scans by plate number. Farivar then went to city councilmembers and asked them if he had permission to run their plates through the tool. For those who complied, the data told quite a complete picture of their movement through the city: Scans were clustered around their homes and workplaces — even their favourite restaurants and bars.
The scanning of plates isn’t really the issue. Police have used these kinds of surveillance techniques for years, and were manually tracking cars and plates long before cameras. The problem is that all this data is accumulating at police departments, and very little of it is being used to bust criminals. The “hit rate” is less than one per cent in most cities. Yet police often refuse to destroy the other 99.5 per cent of the information because they claim it might be used in ongoing or future investigations. The ACLU thinks that 48 hours is an adequate amount of time to search and scrub the data, which would eliminate the problem of anyone being able to access it later, much in the way Ars Technica has illustrated it can be.
Meanwhile, tens of thousands of cameras are rolling, collecting and storing one of the largest databases in the country of very personal, highly specific location-based information. If Farivar could access the data for his journalistic experiment, then anyone could do the same for more nefarious purposes. It’s scary to think what might happen to this data the wrong hands. [Ars Technica]