The infamous Silk Road resurrected itself like a junkie phoenix this month, leaving its long-time residence on Tor for a new anonymizing service called the Invisible Internet Project, or I2P. News of the high-profile dark market’s new address nudged the little-known I2P into the spotlight. Now, after a decade in the dark, the project is emerging as an alternative destination for cybercrime, and a strong complement or even alternative to its older sibling Tor.
Silk Road Reloaded isn’t the only criminal I2P news this month. Security experts recently warned that a nasty ransomware called CryptoWall has launched an updated version of its digital shakedown scheme using I2P. The program encrypts its victims’ files and then demands money — cryptocurrency — to decrypt them. The ransomware scheme originally just used Tor to anonymize its traffic, and as a landing page for its extortion payments. Now it’s migrated to I2P.
It makes it sound like the invisible internet is online version of the most dangerous part of town — a dank digital alley you’d only go down if you want to buy drugs or rob someone. In reality, the service isn’t so sketchy. It was created as a friendly peer-to-peer communications hub, not a teeming, seedy digital underbelly. Let me explain.
Internet inside the internet
I2P is the very deep web. The software project hosts sites that are not accessible through general search engines like Google, and, like Tor, anonymizes traffic by ping-ponging it from proxy to proxy. Every machine using I2P acts as a router, which makes I2P a fully decentralized service. This is a security strength, since traffic can travel down different network paths in a way that frustrates any attempts at man-in-the-middle attacks. All traffic is encrypted end-to-end.
But unlike Tor, it’s a terrible way to anonymously browse the internet outside of I2P, and by terrible I mean completely useless. I2P isn’t designed to let you look at the BBC or YouPorn or UnicornsShitting.com anonymously. It’s designed to let you browse “eepsites” which are the sites hosted within the I2P intranet. This is a key distinction, and a reason why I2p and Tor are really more complementary services than rivals when it comes to web browsing.
What’s more, you need to download special software to access the network. It’s easy to install but hard to navigate, and the steeper learning curve has kept the I2P community small and tight-knit since its 2003 beginnings. Most of the creators go by pseudonyms and talk with each other and with users on an intimate IRC scene with extensions that allows people to directly chat without a middleman server. They don’t make money and haven’t organised into a non-profit.
Here’s how underground I2P still is: The Electronic Frontier Foundation, a leading advocate of online privacy, hasn’t really bothered investigating the 12-year-old anonymizing service yet.
“I haven’t found anyone who has taken an in-depth look at I2P yet,” EFF media relations director Rebecca Jeschke told me in an email. “In general, folks here think I2P is a promising project. It’s really important to have a variety of strong solutions for anonymity, privacy, and security online. However, folks did say that for practical use today, Tor is far ahead in terms of implementation and reliability.”
A safer way to torrent
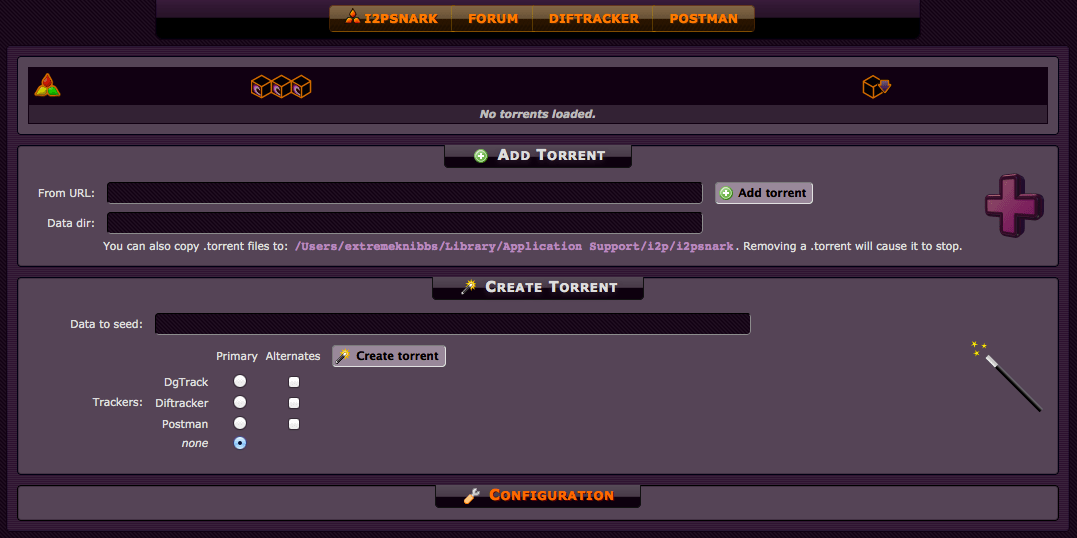
I2P started as an offshoot of Freenet, perhaps the first anonymizing tool on the internet, and it still has a Web 1.0 aesthetic and sensibility. It remains, in essence, a more secure way to share torrents. The torrenting system is well-built and easy-to-use, and peer-to-peer sharing is the backbone of the entire service. It’s a much better place to score a digital copy of Guardians of the Galaxy than any sort of drug.
If you use torrents and you’re worried about getting fingered by the long hand of the law, I2P is worth downloading for that reason alone. Developer and I2P press liaison Jeff Becker said the entire system would have to break down for someone to get caught torrenting on I2P — which of course doesn’t mean it absolutely couldn’t happen, but it’s safer than doing it without an anonymizing service.
Not a bustling haven for drug markets
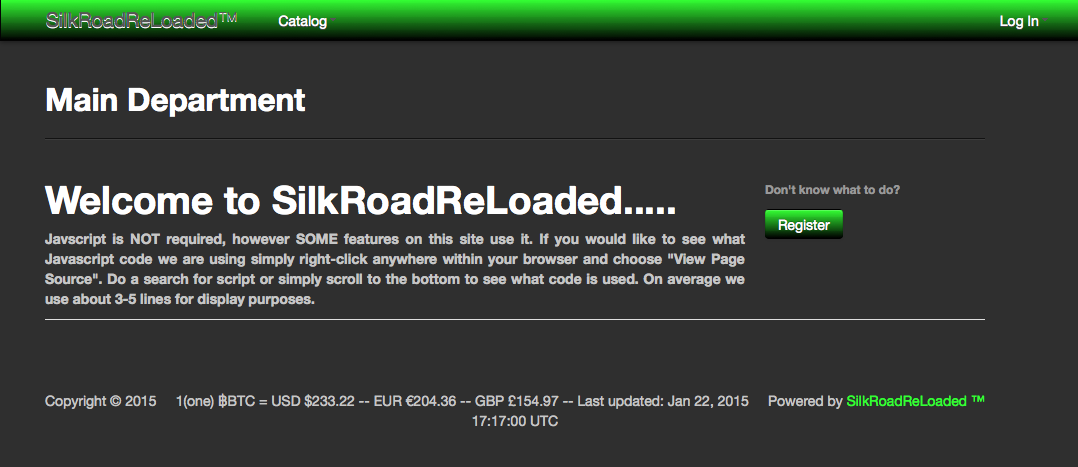
That said, portraying I2P as the new destination for all things hidden and illegal online is also simply not true. The Silk Road Reloaded remains near-empty, and Becker said that, contrary to reports that it recently sprang up, the “new” drug market has been around for over a year.
Also, the Silk Road brand is dead at this point. Darknet experts warn that anyone still trying to milk credibility from the name is probably looking to rip people off, and reports from darknet users suggest that this I2P Silk Road is almost certainly a scam. Meanwhile, the most prominent contraband marketplace on I2P, creatively named TheMarketplace, never had many vendors and shut down a few months ago.
If this is the new digital drug playground, it’s a forlorn, empty one.
Should you use it?
I2P has the potential to act as an anonymizing service for a great range of applications. But it has not had its architecture tested in the way that Tor has, and characterising it as a holy grail of anonymity is a dangerous mistake.
The project is still an incredibly small venture with a fraction of Tor’s users and a DIY-minded community of independent developers behind it; unlike Tor, I2P has never received funding from the U.S. government. All that said, if you do decide to give it a whirl, here are some things to keep in mind.
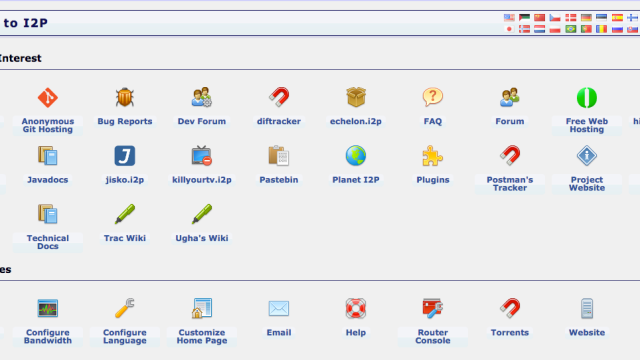
Downloading the software is not an involved process, but afterwards you’ll need manually reconfigure your browser before you’ll see the landing page appear, which is annoying but not tough. Each browser has slightly different method but they mostly involve changing your proxy port settings. The I2P website walks you through how to do this. Once you get to the homepage, you can browse the highlighted eepsites, including an FAQ, an I2P version of Pastebin, torrenting sites and forums, and a list of other sites.
Apart from the sites highlighted on the landing portal or in its Address Book, you can’t automatically access other sites, even if you have their .i2p address. To get on the (bullshit) Silk Road Reloaded, for instance, you need to know its Base 64 or Base 32 address, another string of letters and numbers. It’s not easy to track this shit down; I had to browse through the comments on a Reddit post to find the address I needed to log in.
I2P is still a niche, underground tool right now. But an interesting one to watch. If the FBI reveals a serious Tor weakness during the Silk Road trial underway (which might happen if it explains how the agency traced Ulbricht), we could see some migration to I2P. The small-scale service isn’t poised to replace Tor, but it is heartening evidence that we’re not putting all of our anonymising eggs in one underground basket.