We’ve seen eavesdropping issues in Chrome before, like one exploit that lets sites ask for permission to the microphone, and then keeps listening long, long after. But now a new one discovered by Guy Aharonovsky goes a step further: it triggers listening with no permission, even if your microphone is completely disabled.
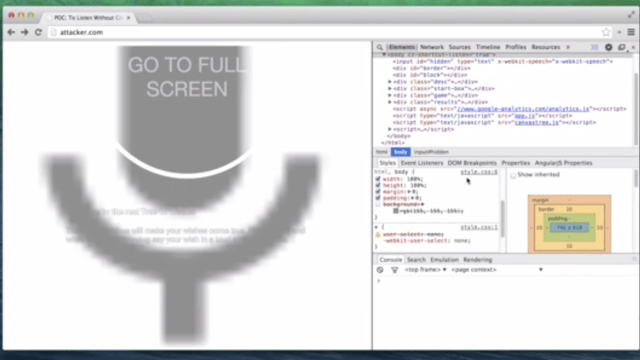
The trick is deceptively simple on its face: essentially an attacker can turn an entire website into one, big, invisible record button and then just listen away. But in practice, it relies on two other tricks. The exploit makes use of Google’s old speech API that doesn’t indicate microphone use in the address bar for instance, but rather in a bubble that can be conveniently obscured from view.
Guy whipped up a (truly bizarre) demo of the exploit that’s optimised from Chrome on OS X, but claims it can be easily tweaked to run on any flavour of Chrome. Likewise, the demo leans on fullscreen mode to completely obscure the listening bubble, but that’s just a matter of convenience, not necessity.
This exploit requires quite a few things to go right in order to fool folks, but if nothing else it’s a reminder that maybe you shouldn’t be saying your passwords out loud while you’re typing them, or spilling your deepest secrets to your computer screen. [Guya via Alex Goldmark]