The hacking scenes in House of Cards are wildly unrealistic. They’re everything from infuriating to hilarious, but they are definitely not surprising. It turns out that this long tradition of portraying hacking horribly, horribly wrong in TV and film is often intentional.
In fact, in a lot of ways it’s necessary.
Real hacking is boring
Good TV should be fun to watch. Movies should be fun to watch. Real-life hacking? Not so fun to watch.
TV hacking:
Real-life hacking:
Movie hacking:
Real-life hacking:
So forgive Hollywood if they try to spice things up with pretty flashing lights and frenzied typing. After all, it’s basically impossible to film accurate hacking and have it be visually interesting in the way film demands.
There’s a whole host of problems, starting with how screens during real hacking don’t necessarily have any motion, and static data display is boring on the big screen for any amount of time longer than a second. The matter is made worse by how most hacking software is function over form, whereas interesting action scenes demand the exact opposite. Add that to tiny text sizes that are unreadable at any reasonable filming distance, and you’ve got a pretty good argument for replacing it all with some flashing lights and colours.
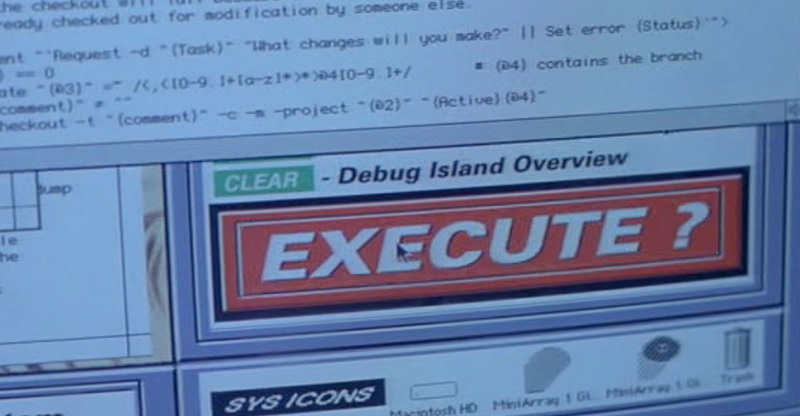
The same goes for sound. The only way to make footage of an unreadible static screen less interesting would be to score it with subtle typing noises, and maybe contemplative breathing. Which explains why movie hackers are always pounding on the world’s loudest keyboards with hammer-fingers, and why each and every program screams with bleeps and bloops whenever you so much as move the mouse. You know, on the rare occasion there is a mouse, because watching cursors move is also pretty boring.
Let’s try a little experiment. First watch a supercut that shows off the worst hacking:
And now try a tutorial on cracking WPA passwords:
One of them is fun to watch.
But that’s just for starters. Even if every packet-sniffer application was adorned with all the ASCII skulls and mandatory green-on-black text in the world you’d still have a problem.
Real hacking is almost never action the way that Hollywood needs it to be. Hacking is more often just arduous research, planning, and then a computer trying a whole bunch of things on its own for hours. Cracking into someone’s email account in real life is invariably 10-second victory built up to by hours if not days of painstaking detective work and computers running brute-force crackers. Trying to film hacking as high-tension is like trying to film a stakeout as an action scene. The sum-total of hours of tedium.
There are a few very specific exemptions to this; just spend a couple of minutes staring at a real-time visualisation of what a DDoS attack looks like, or bots being deployed, and you can see how it might fit in a movie or TV show.
But those very particular cases rarely align with whatever impossible techno-wizardry writers need to move the plot from point A to point B, preferably in a matter of minutes. As far as the stories are concerned, hacking is less of an interesting thing to be portrayed realistically, and more of a convenient place to make impossible things convenient by screaming “TECHNOLOGY!!!!!”
Besides, even if hacking were thrilling in real life, it would still be confusing as hell.
Real hacking is complicated
What’s worse than boring? Boring and confusing. In theory, a lot of the most common go-to hacks out there are very very simple. DDoS attacks just flood the target with more information than it can handle. Password crackers just try passwords over and over again until they get something right. Packet-sniffers just peek at incoming and outgoing traffic on a network in case something interesting happens.
The specifics are another story. Take, for instance, Wikipedia’s explanation of SQL injection:
A code injection technique, used to attack data driven applications, in which malicious SQL statements are inserted into an entry field for execution (e.g. to dump the database contents to the attacker). SQL injection must exploit a security vulnerability in an application’s software, for example, when user input is either incorrectly filtered for string literalescape characters embedded in SQL statements or user input is not strongly typed and unexpectedly executed. SQL injection is mostly known as an attack vector for websites but can be used to attack any type of SQL database.
“But wait!” you say. “If the point is just to have incoherent technobabble why not have remotely accurate incoherent technobabble? Why can’t it just be something that doesn’t drive me up the wall!? I mean tracking the killer’s IP address through a GUI programmed in Visual Basic?! Are these people insane?!”
Now you’re getting to the heart of it….
They’re in on the joke
Ever heard the Wilhelm Scream? You almost definitely have. Born as a soundbyte for the 1951 film Distant Drums, it’s distinctive, campy and…really not that convincing of a scream. Still, it’s been in over 200 movies.
It’s an inside joke, passed down through generations from director to director. So is bad hacking. An anonymous Redditor who claims to have written for one of the biggest offenders explains it best:
We write those scenes to be inaccurate and ridiculous on purpose.
I’m a young writer in his mid-30’s, computer and game savvy. Lots of us are. I guess you could call it a competition of one-upping other shows to see who can get the best/worst “zoomhance” sequence on the air. Sometimes the exec producers and directors are in on it, and other times we just try to get bits and lines into scripts.
90% of our TV viewing audience will never know the difference and honestly, we love it when threads like this get started and love reading the youtube comments.
It’s an anonymous source, so take it with a grain of salt, but it also makes complete sense. Hollywood hacking scenes don’t just throw rules of hacking out the window; often they don’t even adhere to the most basic rules of technology that the writers probably have in their very own homes.
In the past, things might have been a little different. In, say, the WarGames era you might be able to believe that the folks who worked up the screenplay might not really have a grasp on the way computers are connected (and not connected) through the internet.
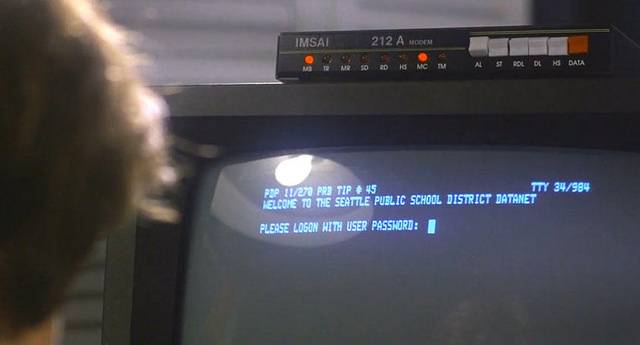
But nowadays basic computer and internet knowledge is more of a necessity than it has ever been. If you see something too dumb to believe, it’s probably a joke. Or at least a setup; the punchline of which is when you lean over to your date and exasperatedly explain that there’s no way that could happen since no CTO worth his salt would ever let that kind of information be remotely accessible instead of just relegating it to an isolated intranet, and besides that’s not actually what VPNs do.
They’re not that stupid; they are just trolling you. And really, what could be more hacker-savvy than that?
Picture: ra2studio/Shutterstock
